Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
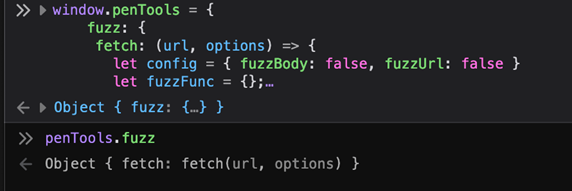
Mission Imfuzzable: How to Fuzz Web Apps you can't Intercept
Introduction Fuzzing is a critical technique for finding vulnerabilities in web applications by efficiently trying a large volume of different inputs. Typically, we capture the legitimate request in our interception proxy (Burp, ZAP, etc.) and use its fuzzing tools to repeat that web traffic with ...
Continue Reading
Never miss a Professionally Evil update!
Understanding Server-Side Template Injection (SSTI)
Testing |
Training |
QA |
web penetration testing |
penetration testing |
application security |
OWASP |
web application security |
methodology |
OWASP Top 10
Web applications play a vital role in delivering dynamic content to users. To achieve this, ...
Continue Reading
Introducing SamuraiWTF 5.3: A Powerhouse for Web App Pen Testing
Testing |
Training |
samuraiWTF |
web penetration testing |
application security |
professionally evil |
Secure Ideas |
hacking |
OWASP |
Project
We are thrilled to announce the release of SamuraiWTF (Web Training Framework) version 5.3! This ...
Continue Reading
ZAPmas Feedback
Testing |
open source |
web penetration testing |
OWASP |
mobile application |
web application security |
API
Sometimes Christmas comes early, and in this case for me it was the publication of the Twelve Days ...
Continue Reading
12 Days of ZAPmas - Day 12 Testing a new Content-Security-Policy
What is the CSP? The Content-Security-Policy (CSP) is a widely recommended control and is ...
Continue Reading
Application Security 202: Vulnerabilities Accepted
Testing |
Vulnerability |
Guidance |
data breach |
information security |
penetration testing |
application security |
professionally evil |
Secure Ideas |
hacking |
best practices |
cybersecurity |
Privilege Escalation
vul·ner·a·bil·i·ty The quality or state of being exposed to the possibility of being attacked or ...
Continue Reading
ViewState XSS: What's the Deal?
Testing |
developers |
QA |
security |
testers |
web penetration testing
As penetration testers, there are many different technologies that we have to be familiar with. The ...
Continue Reading
Testing ASP.Net WebForms: Request Method Validation
As a professional penetration tester, there are many features of an application that are similar ...
Continue Reading
Has contents: true
Total pages: 1
Current page: 1
.png)