Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
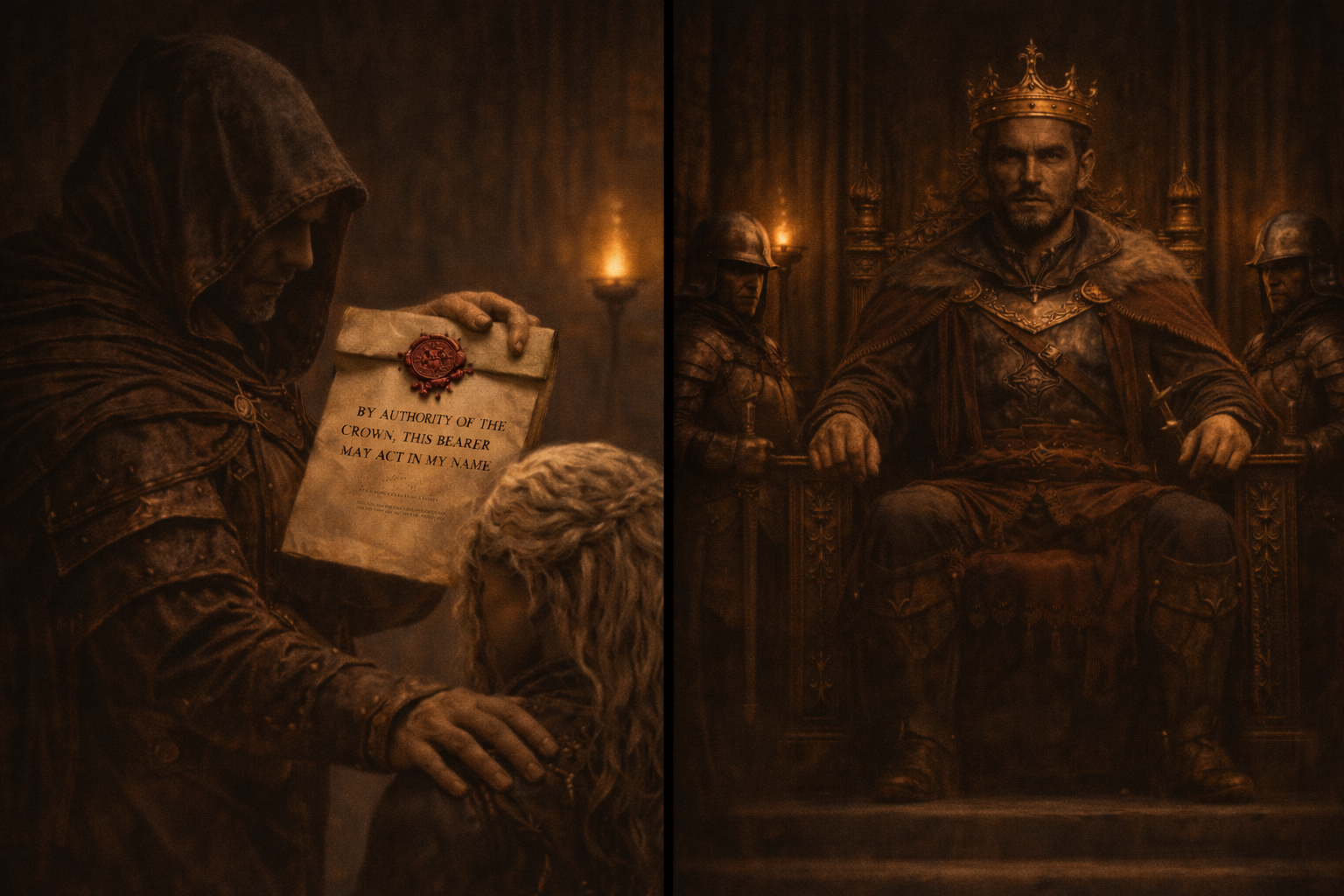
Paths to Power in Active Directory Part 5: ESC6 - Under a False Sigil
In Part 3, ESC2: The Seal of Any Purpose, we shifted from identity to capability. Instead of changing who a certificate represents, ESC2 explored how broadly that certificate can be used once issued. In Part 4, ESC3: In the Name of the Crown, we moved into delegated authority. Rather than ...
Continue Reading
Never miss a Professionally Evil update!
Paths to Power in Active Directory Part 4: ESC3 – In The Name of The Crown
In Part 2, ESC1: No One, Yet Everyone, we examined a misconfiguration that allows a low-privileged ...
Continue Reading
Paths to Power in Active Directory Part 2: ESC1 – No One, Yet Anyone
This is the second post in this series. Part 1 can be found here.
Continue Reading
Application Security 202: Vulnerabilities Accepted
Testing |
Vulnerability |
Guidance |
data breach |
information security |
penetration testing |
application security |
professionally evil |
Secure Ideas |
hacking |
best practices |
cybersecurity |
Privilege Escalation
vul·ner·a·bil·i·ty The quality or state of being exposed to the possibility of being attacked or ...
Continue Reading
Privilege Escalation via File Descriptors in Privileged Binaries
application security |
professionally evil |
Secure Ideas |
Linux |
programming |
File Descriptors |
SetUID |
Privilege Escalation
Today I wanted to cover an application security topic that applies to SetUID binaries. As we all ...
Continue Reading
Has contents: true
Total pages: 1
Current page: 1