Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Your Risk Framework Is Broken: The Al Reality Check Every CISO Needs
Every risk management framework in cybersecurity relies on the same fundamental equation: Risk = Likelihood x Impact. But what happens when one half of that equation becomes meaningless overnight? If your organization uses any of the major cybersecurity risk assessment frameworks like NIST SP ...
Continue Reading
Never miss a Professionally Evil update!
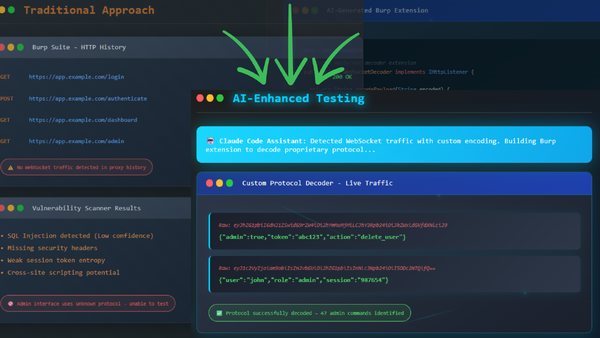
The Real AI Revolution in Penetration Testing
Custom Tooling at Lightning Speed Most cybersecurity professionals hear "AI in penetration testing" ...
Continue Reading
Introducing BILE - Groundbreaking Classification for Web App
Training |
penetration testing |
OWASP |
web application security |
BILE |
OWASP Top 10 |
BILE Classification Scheme |
vulnerability classification
As a seasoned web application penetration tester, I've always felt that there should be a more ...
Continue Reading
Introducing PETaaS®: Professionally Evil Testing as a Service
We're thrilled to announce the launch of our latest offering: Professionally Evil Testing as a ...
Continue Reading
Ace CISSP Exam Prep with ChatGPT: Your AI Study Buddy
Are you preparing for the CISSP exam or any other exam that requires a deep understanding of ...
Continue Reading
Why we ditched LastPass
LastPass is a very popular password management service with both personal and business solutions. ...
Continue Reading
Hunting Secrets
Applications are hemorrhaging sensitive data. In many cases, the culprit is marketing and analytics ...
Continue Reading
Why your application needs a Content Security Policy (And How to Build One)
As a web application owner, it is crucial to understand the concept of a content security policy ...
Continue Reading
Announcing Burp Co2!
This is for those of you who do web pen testing with Portswigger’s Burp proxy tool! Over the past ...
Continue Reading
How to configure Android (Virtual) for Mobile PenTest
Setting up your environment for a mobile application penetration test can be a chore, especially if ...
Continue Reading
Cooking up Better Security Incident Communications
I am fond of meal kits. I enjoy the entire experience: the scrolling through delicious-looking meal ...
Continue Reading
Once upon a time there was a WebSocket
This is the story from one of our recent penetration testing engagements. Still, the story is a ...
Continue Reading
Has contents: true
Total pages: 3
Current page: 1