LastPass is a very popular password management service with both personal and business solutions. Recently, LastPass has experienced mounting criticism from the information security industry as a result of an incident described in an August 25, 2022 blog post. The blog post was updated in November, and then again on December 22, 2022, with each update seeming more ominous than the last. In their most recent update, LastPass appears to contradict itself on a technicality:
While no customer data was accessed during the August 2022 incident, some source code and technical information were stolen from our development environment and used to target another employee, obtaining credentials and keys which were used to access and decrypt some storage volumes within the cloud-based storage service.
To me this reads as both no customer data was accessed initially, yet sufficient information was stolen to target an employee, resulting in storage volumes being decrypted and accessed. To form an analogy: "while the bank robbers didn't take anything belonging to customers, they stole the keys to the vault which was used at a later time to gain access to customer valuables". It is technically accurate, yet a semantic contradiction. Those storage volumes contained backups of data that was accessed by a third party, specifically (again from the LastPass blog):
The threat actor copied information from backup that contained basic customer account information and related metadata including company names, end-user names, billing addresses, email addresses, telephone numbers, and the IP addresses from which customers were accessing the LastPass service.
The LastPass blog continues to describe how, in addition to all the above information, a copy of the customer vault data (i.e. that's the customer's encrypted passwords and other data) was also obtained by the third party. In addition, LastPass makes several statements downplaying the severity of stolen vaults and they have also never made it clear exactly which fields were encrypted and which weren't (e.g. we still don't know if notes were encrypted). You can read 1Password's blog post Not in a Million Years to better understand how your password vault may be more crackable than LastPass claims.
As with any password manager, the entire business model of the LastPass solution is to provide a more secure and user-friendly solution to passwords than having people try to manage their own. The passwords in question are what protect virtually all personal data that is accessed on the Internet. As a consequence, customers should be able to trust their password manager to take better security measures than just about any other type of service or product they interact with online.
While I appreciate it when a company makes the effort to disclose the results of their incident investigations, I don't agree with using technical jargon and conjecture to mislead customers into a false sense of security. This "it's not so bad" attitude combined with the numerous LastPass breaches over the last few years has eroded the trust necessary for LastPass to be considered a viable solution. In my opinion (personal and professional) this is "bad enough" and LastPass, you failed at the one thing you are supposed to be good at: protecting my passwords.
We were again reassured that moving away from LastPass was the right thing to do when we attempted to cancel our account. This was done by first filling out the following form:
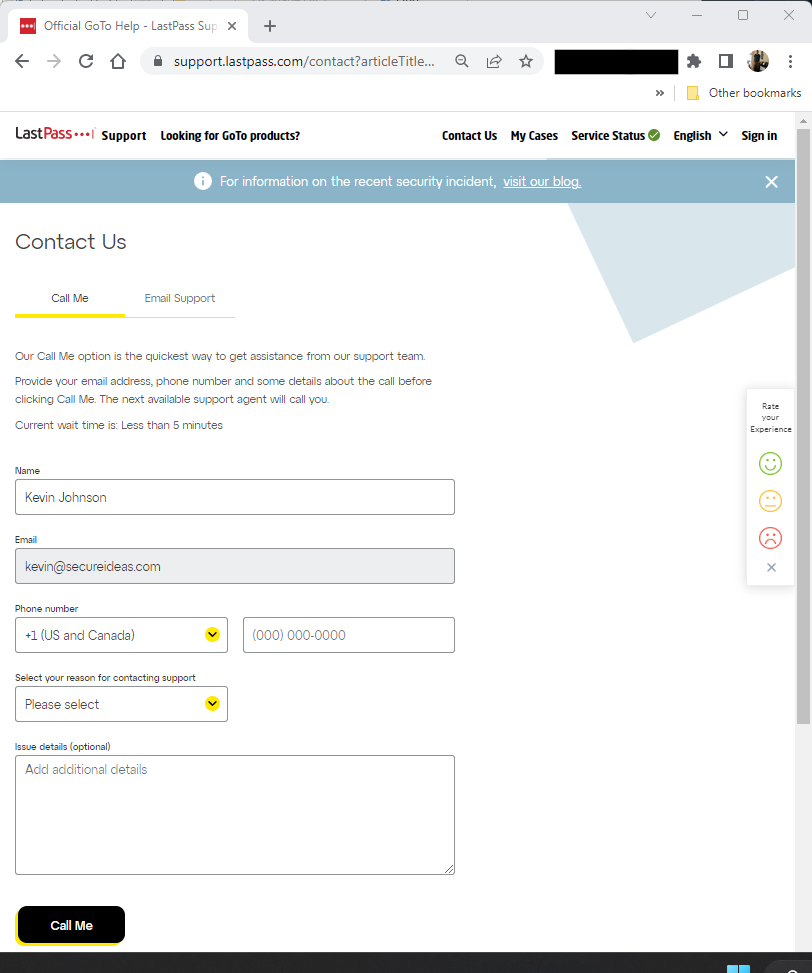
Notice that Kevin is not signed in. He received a phone call to the number he provided on this form, and the conversation went something like this:
LastPass: Hello this is LastPass, how can I help you today?
Kevin: Hi! I would like to cancel my autorenewal.
LastPass: And your name is?
Kevin: I am Kevin Johnson
LastPass: And your email address?
Kevin: kevin@secureideas.com
LastPass: Are you an admin on the account?
Kevin: Yup
LastPass: Thank you. We have canceled your renewal.
Admittedly there was a little bit more to the conversation regarding our reasons for canceling, but the takeaway here is that we were able to make an account change without authenticating ourselves in any way. Furthermore, I am the account owner and did not receive any email notification of this change to my account. LastPass does not seem to have a grasp of foundational security concepts.
Fortunately, there are several alternative password managers that we deem to be more trustworthy and that have similar features, price, and functionality to LastPass. Most of them can even import passwords from a Lastpass export file. The only downside is the need to migrate to a different solution. However, since we have already decided to treat our vaults as if they may ultimately be cracked, we are already doing a large number of password changes. Relatively speaking, there's only a little extra effort required to change those passwords in a different password manager.
Wondering what an attacker could do with your organization's credentials?
Weak password management, credential reuse, and exposed vaults are exactly the kinds of things our team tests for. If you want to understand your organization's exposure to credential-based attacks, we can help.
Get in Touch