Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
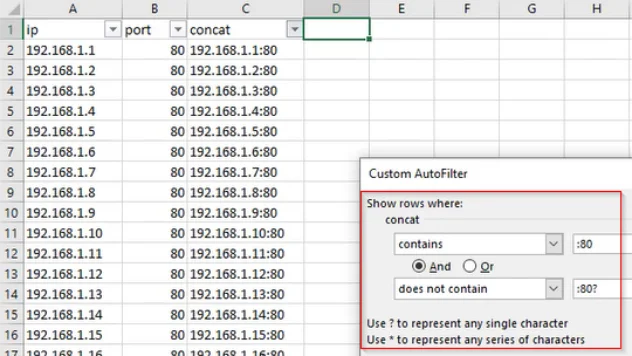
Working With Data: IP and Port Filtering
Training |
professionally evil |
Secure Ideas |
technology tips and tricks |
sysadmin |
data |
data manipulation |
excel |
spreadsheet |
filtering
During our day-to-day work, there's a lot of data that we interact with. In order to make good use of it, you need to be able to work with it in a way that makes sense for the task at hand. In today's example, we're going to consider a situation where the expected scan output contains IP addresses ...
Continue Reading
Never miss a Professionally Evil update!
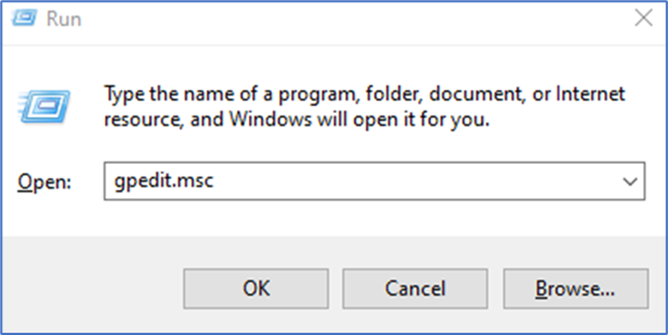
How to allow multiple RDP sessions
Training |
penetration testing |
pentesting |
Windows |
technology tips and tricks |
rdp |
sysadmin |
system administration
The goal of this article is to walk through how to set up a Windows host to allow multiple remote ...
Continue Reading
PowerShell Tips: How do I Mount a VHD or Lock a BitLocker Drive?
encryption |
security |
professionally evil |
Secure Ideas |
getting started |
BitLocker |
VHD |
rtfm |
manage-bde |
mount-vhd |
manage bitlocker |
technology |
technology tips and tricks |
Windows 10 |
VHDX |
encrypted drive |
technology tips |
how-to |
btfm |
Windows 11
PowerShell Tips How do I Mount a VHD or Lock a BitLocker Encrypted Drive?
Continue Reading
Has contents: true
Total pages: 1
Current page: 1