PowerShell Tips
How do I Mount a VHD or Lock a BitLocker Encrypted Drive?
Anyone who has worked in a technical position for any length of time will have a collection of tips and tricks that they've accumulated over time, myself included. This is one reason why we tend to see so many RTFM and BTFM related books and resources being released. And really, there's a lot to keep track of, so this is a natural result of having to deal with so many different types of tools and technologies.
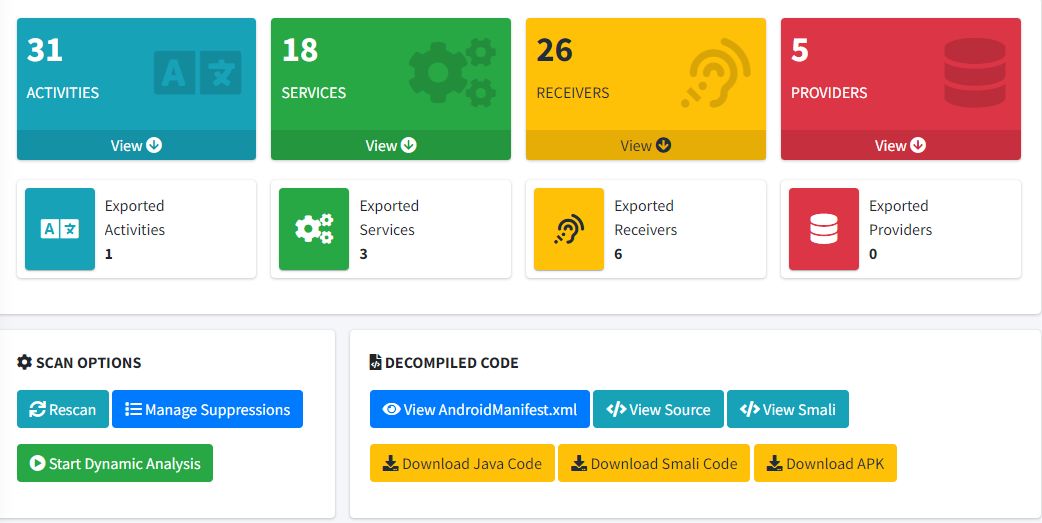
For today, I'd like to look at a few tidbits of PowerShell knowledge that may help make life easier for anyone who needs to quickly mount or lock a BitLocker encrypted drive. If you're uncertain of how to set up a Virtual Hard Disk (VHD) file and encrypt it, then you can visit a short article located on our blog pages. Keep in mind that while this article was written for Windows 10, it works for Windows 11 as well.
Tip #1 - Mounting a VHD drive
Occasionally, VHD drives may not show up when the computer is rebooted and, while it's not difficult to manually click through the Disk Management options for remounting, having a script to run makes the process faster and more efficient. This also allows us to make use of these drives as part of scripts for tooling and security.
PowerShell can be used to quickly mount these encrypted drives (VHD, VHDX, etc). Using the Start-Process cmdlet will allow you to start various processes on your computer. When combined with Mount-VHD and the -WorkingDirectory parameter (which allows you to explicitly set the file's source directory), you can easily mount your VHD drive at any time.
For example, the below PowerShell script can be run on-demand:
Start-Process PowerShell -ArgumentList "Mount-VHD -Path 'c:\path\to\vhd\file'" -Verb RunAs -WorkingDirectory C:
(Please note that this will not unlock the drive: it will only mount the drive for you.)
Tip #2 - Locking a BitLocker Encrypted Drive
In dealing with my BitLocker drives, I have always been surprised that the typical right-click menu does not have the lock function for a drive that I have mounted. This is an odd choice for Microsoft, especially with the idea that these drives are encrypted since they contain sensitive data. Therefore, this next tip is intended to leverage a quick PowerShell command which will lock your BitLocker encrypted drive or VHD file.
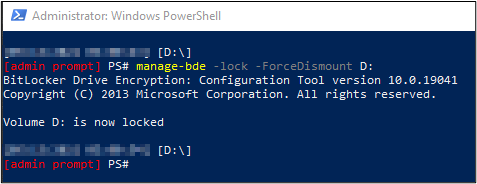
First, run PowerShell with administrative rights. Then, enter the following command:
manage-bde -lock -ForceDismount <Provide the VHD Drive Letter>
The following screenshot is what you should see when the command has been successfully executed. The drive letter referenced will match the one you used in the command:
Bonus Tip - Opening PowerShell in your Current Directory
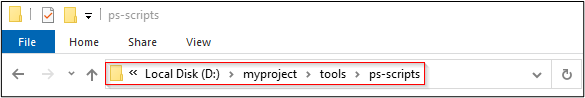
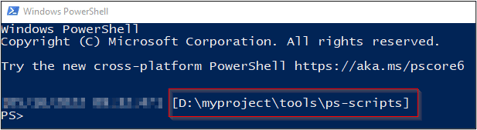
Here's a simple bonus tip to launching PowerShell that came as a surprise to me when I first encountered it. If you want to open a PowerShell terminal from your current directory location, rather than manually navigating via cd commands, then you can:
1. Click in the Windows Explorer address bar (where your current directory location is displayed):
2. Type powershell, and hit Enter:
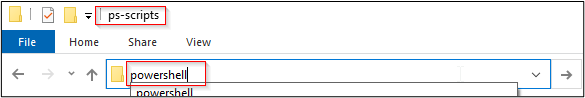
As shown below, a PowerShell terminal will open, which will already be set to that directory location. This is a simple trick, but it's one that I now use on a regular basis.
There are many more PowerShell features available, and our goal is that the ones noted above can help make these types of tasks easier or more efficient. If you're interested in security fundamentals, we have a Professionally Evil Fundamentals (PEF) channel that covers a variety of technology topics.
Need help securing your Windows environment?
BitLocker configurations, PowerShell security, and Windows hardening are all things our team evaluates during a penetration test. If you want to know where your systems stand, reach out.
Get in Touch