Testing In Mobile Applications
In today’s world, the significance of mobile applications in our daily lives is undeniable. As these applications continue to saturate more and more of our personal and professional lives, the importance of ensuring their security has also grown. This is where penetration testing, a key component of cybersecurity, comes into play. While it shares similarities with web applications, mobile penetration testing is unique in some ways and often requires a different approach.
At its core, penetration testing involves the deliberate simulation of attacks to pinpoint vulnerabilities in software systems. These types of activities serve as a proactive measure against real-world security breaches. Whether applied to web or mobile applications, the primary objective is to fortify the protection of sensitive data and preserve the integrity of the applications.
Unlike web applications, which primarily operate in a browser environment, mobile apps such as iOS or Android interact more closely with the underlying operating system. This interaction can potentially expose the system to additional security threats. Furthermore, layers of complexity are added when you consider the different combinations of operating systems and mobile hardware being used. The way in which mobile apps handle data, manage permissions, and interact with other applications can also differ dramatically from web applications. These differences are not just in the surface-level features but extend to the core architecture and security considerations.
Considering the additional nuances to mobile application tests, we want to highlight some of the key considerations. This will include an evaluation of the client portion of the mobile apps, excessive permissions, and storage management.
When delving into mobile application security testing, it is important to familiarize yourself with tools like MobSF, and how issues relating to certificate pinning affect your ability to proxy mobile traffic. A thorough understanding of both the similarities and differences between mobile and web application testing is not only useful for cybersecurity professionals, but also for mobile app developers, project managers, and anyone else who is involved in the development or security of mobile applications.
Evaluating the Client Portion of Mobile Applications:
A Key Aspect of Penetration Testing
For most applications, the client portion has the largest impact on user experience. This is generally the first part of a mobile application testers will interact with during an engagement. The client side is also where we will often see many of the similarities between web and mobile applications. These similarities include items such as authentication and authorization, input validation, output sanitization, secure configuration practices, data storage, and more. It is important to keep in mind that this is not universal, and we are likely to find several notable differences.
When assessing the client side of a mobile app, it is important to examine the permissions required. Oftentimes mobile applications have overly broad or excessive permissions than is necessary for their functionality. Excessive permissions also contradict the industry's best practice of providing the least amount of privileges necessary. Mobile application developers should ensure that only the minimum amount of access should be granted in order to perform the required task. Expanding the access given to mobile applications will significantly increase its overall attack surface. An application that unnecessarily requests access to contact lists or location services can quickly become a conduit for data leakage or unauthorized surveillance if exploited by malicious actors.
Another essential aspect to consider is the safe versus unsafe storage of secrets within the application. Secrets, such as API keys, tokens, and passwords, must be stored securely to prevent unauthorized access. Unsafe storage practices, like embedding secrets within the source code, storing account credentials in the application’s manifest file, or simply using easily accessible local storage, make the application susceptible to exploitation. These types of insecure practices are sometimes missed during the mobile application development process, making it even more important to thoroughly evaluate the secret storage mechanisms being used.
An example of a unique challenge found when dealing with mobile apps is the hijacking of implicit Android intents, which are used to facilitate inter-component communication. However, if these are not properly managed, then they can become a vector for attackers to read sensitive information, inject malicious data, or gain unauthorized access to application components. If implicit intents are needed, then any sensitive information should be removed. While this type of flaw is more commonly found in older versions of Android, it emphasizes the need to implement a robust development framework to enforce secure coding practices. Additionally, a thorough assessment of the inter-process communications taking place within your mobile application is essential for detecting and mitigating potential risks.
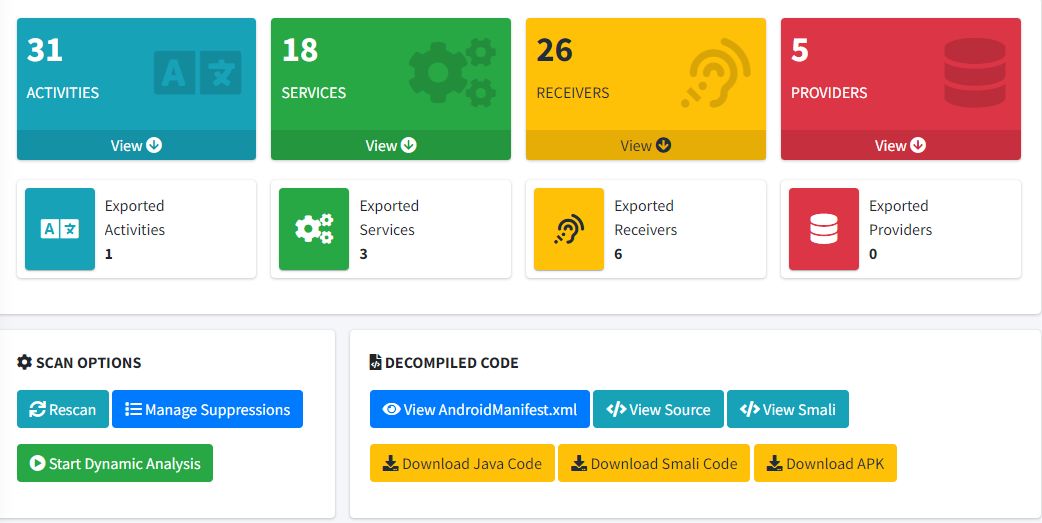
To effectively assess a mobile app for vulnerabilities such as these, penetration testers often employ a combination of static and dynamic analysis tools. One such tool is the Mobile Security Framework (MobSF). When leveraged for static analysis, MobSF can be used to automate the process of identifying security loopholes in the source code and binaries of mobile applications. It provides a comprehensive suite of features that allow testers to uncover issues related to insecure code practices, improper handling of user data, and potential vulnerabilities that could be exploited through reverse engineering. By integrating tools like MobSF in the evaluation process, testers can more efficiently pinpoint and address security risks in the client portion of mobile applications.
Assessing the client-side aspect of mobile applications extends beyond the identification of immediate vulnerabilities. It’s a proactive approach to understanding and mitigating the broader spectrum of potential security risks. Ultimately, this phase of testing serves as the foundation for a secure mobile application, ensuring that the user-facing side of the app is hardened against commonly found security flaws.
Certificate Pinning in Mobile Application Penetration Testing:
Balancing Security and Practicality
The next area we want to cover is the topic of certificate pinning. Certificate pinning is a security measure employed by mobile applications to ensure that they communicate only with the intended server. By embedding either the server's certificate or its public key within the application, it validates the server's identity and establishes a trusted connection. This provides an effective mitigation against man-in-the-middle (MITM) attacks. In scenarios where certificate pinning is viable, such as applications that are not required to operate within corporate networks using TLS inspection, it serves as an excellent control mechanism, enhancing the app's defense against interception and unauthorized data access.
Conversely, certificate pinning also introduces certain complexities when it comes to penetration testing. The primary objective is to simulate realistic attack scenarios and uncover potential vulnerabilities. Mobile application pentests are typically performed under strict time constraints. In order to facilitate more thorough testing during these limited timeframes it is necessary to proxy traffic, which is prevented by certificate pinning. Disabling certificate pinning during these tests is a strategic decision. It is not a suggestion of the control's ineffectiveness but instead it works off the assumption that, given enough time and resources, an attacker could potentially bypass it. By disabling it, we save penetration testers a significant amount of time and effort which would otherwise be spent attempting to circumvent these types of controls.
This approach allows testers to focus on more critical aspects of the application's security, ensuring a thorough and efficient testing process. It is essential to remember that one of the main goals in penetration testing is not to challenge every security control but to identify and address vulnerabilities in a practical and time-effective manner.
While certificate pinning is a valuable security control in mobile applications, its role in penetration testing is nuanced. Recognizing its strengths and limitations is a key aspect of effectively balancing security needs with the practical aspects of testing.
Proxying Applications: Traffic Analysis
The ability to proxy applications is an essential part of assessing the security of mobile apps, allowing testers to examine the data transmitted between the application and its servers. When comparing Android and iOS, in recent years it has generally become easier to intercept and analyze application traffic on iOS applications using an iPhone or iPad. This is an important consideration since the fewer hurdles needing to be overcome plays a direct role in the overall efficiency of the testing process.
Proxying a mobile device involves redirecting its network traffic through a proxy server, such as Burp Suite or Zed Attack Proxy. A proxy setup allows the tester to observe, intercept, and modify the requests and responses between the mobile application and its backend services. This is where the details related to packet headers, data flow, and business logic are analyzed. While the specifics may vary depending on the proxy tools being used, the general process consists of three main steps:
- 1. Configure the proxy to listen for traffic on the target port.
- 2. Configure the device to use the proxy and port for its communications.
- 3. Install the proxy server's Certificate Authority (CA) certificate onto the iOS device so that incoming and outgoing HTTPS traffic can be decrypted.
When it comes to adding the CA certificate to an iPhone or iPad, the process is generally straightforward. For example, when configuring the CA for Burp Suite, it’s simply a matter of installing the PortSwigger CA certificate, navigating to the iOS General settings, and enabling the certificate to be fully trusted. By comparison, Android devices rely on the system trust store for validating SSL certificates, meaning that the tester's proxy server CA certificate must be trusted by the device. To accomplish this, CLI tools such as ADB (Android Debug Bridge) are needed to manipulate the Android system into trusting the certificate. It should also be noted that while this process is usually straightforward, issues arising during this stage of the testing process can add hours upon hours of troubleshooting effort. This is often seen on mobile apps when certificate pinning has not been removed prior to testing.
Conclusion: Consolidating Insights for Effective Mobile Application Penetration Testing
There are several factors that need to be taken into consideration to get the most from a mobile test. Each aspect of the process, from evaluating the client portion of mobile apps to the disabling of security controls such as certificate pinning, presents its unique set of challenges and considerations.
During the evaluation of mobile apps, emphasis should be placed on the importance of following best practices, addressing issues related to excessive permissions, and the secure storage of secrets. Specialized tools such as MobSF are often needed to uncover potential vulnerabilities that might be missed during routine development processes.
Additionally, testers should pay attention to certificate pinning features, recognizing its value as an effective security measure while also noting the practicality of disabling it during penetration testing. This approach highlights the need to balance robust security measures with the realities of practical penetration testing needs.
Finally, penetration testers and developers alike will benefit from analyzing mobile traffic using a proxy. When looking at iOS and Android, we saw that the general process of proxying the application communications is essentially the same. However, we noted some distinct differences when looking at the installation of a proxy CA certificate, which is only one step in the overall setup and configuration process. Being aware of these types of differences means that you can proactively address issues that are likely to arise as the result of a mobile application testing engagement.
In summary, the field of mobile application penetration testing is multifaceted, requiring a blend of technical expertise, strategic thinking, and constant adaptation to new challenges. As mobile apps continue to play a crucial role in both personal and professional spheres, the need for rigorous and comprehensive security testing becomes increasingly important.
Additional Mobile Security Reference Material:
Mobile Top 10: https://owasp.org/www-project-mobile-top-10/
MobSF: https://github.com/MobSF/Mobile-Security-Framework-MobSF
Certificate and Public Key Pinning: https://owasp.org/www-community/controls/Certificate_and_Public_Key_Pinning
Pinning Cheatsheet: https://cheatsheetseries.owasp.org/cheatsheets/Pinning_Cheat_Sheet.html
Mobile App Testing Guide: https://owasp.org/www-project-mobile-security-testing-guide/