Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
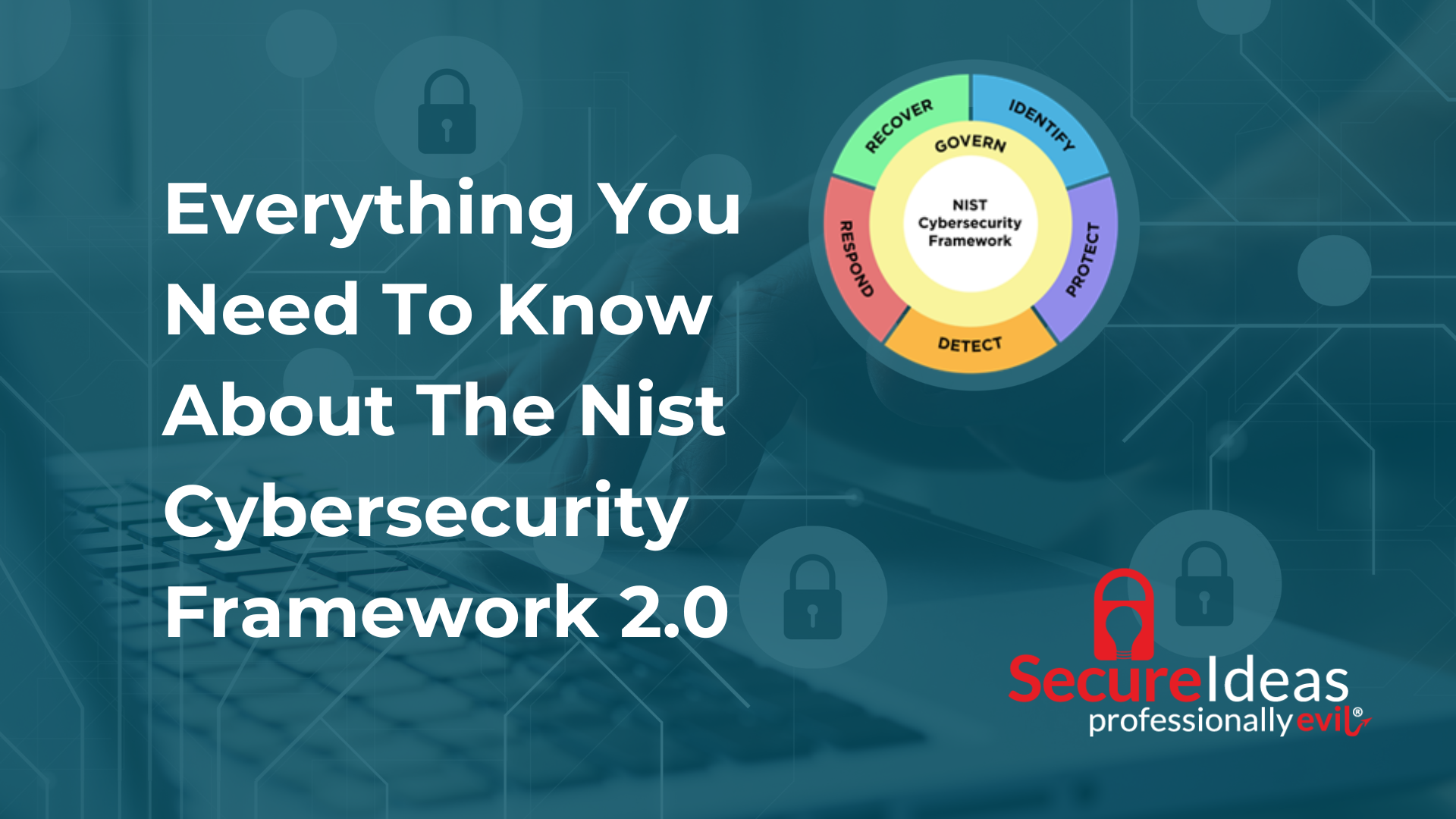
Everything You Need To Know About The Nist Cybersecurity Framework 2.0
best practices |
cybersecurity |
government |
CSF |
cybersecurity standards |
framework |
NIST |
profiles |
tiers
This week NIST released the highly anticipated update to the Cybersecurity Framework (CSF). Here's ...
Continue Reading
12 Hacks of Christmas Day 12: Twelve Drummers Deleting Digital Clutter
🎵 On the twelfth day, clear digital clutter with twelve drummers deleting. Regularly review and ...
Continue Reading
12 Hacks of Christmas Day 11: Eleven Pipers Practicing Safe Browsing
🎵 On the eleventh day, practice safe browsing with eleven pipers practicing. Be mindful of the ...
Continue Reading
12 Hacks of Christmas Day 10: Ten Lords a-Cautious Shopping
🎵 On the tenth day, be cautious when shopping with ten lords a-cautious shopping. Stick to ...
Continue Reading
Nine Ladies Dancin' on Secured Networks
🎵 On the ninth day, keep your network secure with nine ladies dancin'. Protect your Wi-Fi network ...
Continue Reading
12 Hacks of Christmas Day 8: Eight Maids-a-Back-Up Singing
🎵 On the eighth day, safeguard your data with eight maids-a-back-up singing. Regularly backup your ...
Continue Reading
12 Hacks of Christmas Day 7: Seven Swans a-Encrypting
🎵 On the seventh day, protect your data with seven swans encrypting. Encrypt sensitive ...
Continue Reading
12 Hacks of Christmas Day 6: Six Geese-a-Layered Security
🎵 On the sixth day, adopt six geese-a-layered security. Implement a multi-layered security ...
Continue Reading
12 Hacks of Christmas Day 5: Five Golden Updates
🎵 On the fifth day, gift yourself five golden updates. Ensure all your devices and software are up ...
Continue Reading
12 Hacks of Christmas Day 4: Four Calling Bird's Eye View of Scams
🎵 On the fourth day, keep an eye on scams with four calling birds. Be cautious of phishing emails ...
Continue Reading
12 Hacks of Christmas Day 2: Two-Turtle Authentication Unveiled
🎵 On the second day of Christmas, enhance your security strategy with two-turtle authentication. ...
Continue Reading
Has contents: true
Total pages: 3
Current page: 2





.png)

