Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Rolling for Resilience Part 5 - Side Quests: Not Every Member of the Party Swings a Sword!
This is the fifth post in this series addressing my perspective on the current state of Cybersecurity Incident Response training and an approach to improve interest, participation, and expanded learning. Part I can be found here. Part II can be found here. Part III can be found here. Part IV can be ...
Continue Reading
Never miss a Professionally Evil update!
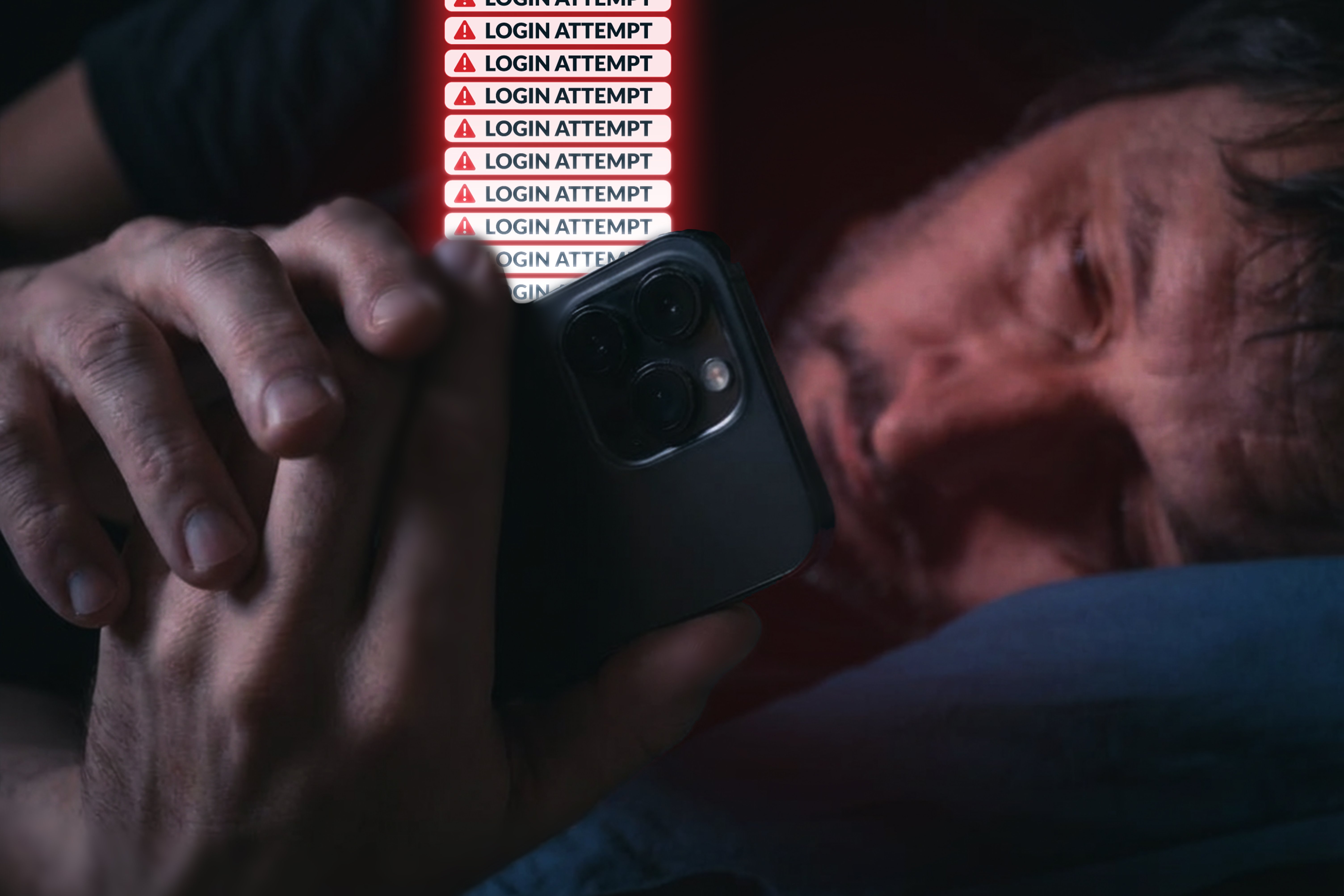
Understanding MFA Fatigue Attacks
Multi-factor authentication has become one of the most widely recommended controls in security. The ...
Continue Reading
Rolling for Resilience Part 4 - Boots in the Field: Manuals for Real-Time Action
This is the fourth post in this series addressing my perspective on the current state of ...
Continue Reading
Supply Chain Security: Trust Is the New Attack Surface
In February 2026, while participating in a panel at IT Expo, one statement kept resonating ...
Continue Reading
Evaluating AI Language Tutors Through a Security Lens
Evaluating AI Language Tutors Through a Security Lens Over the past year or so, I have seen a ...
Continue Reading
Rolling for Resilience Part 3: Battle Prep - The Scrolls of Response
This is the third post in this series addressing my perspective on the current state of ...
Continue Reading
Rolling for Resilience Part 2: The Communication Gauntlet
This is the second post in this series addressing my perspective on the current state of ...
Continue Reading
Rolling for Resilience: A Strategic Guide to Cybersecurity Table-top Exercises
This is the first post in this series addressing my perspective on the current state of ...
Continue Reading
Cybersecurity Essentials for SMBs: Building a Robust Program
When discussions arise around companies' cybersecurity programs, the focus often gravitates towards ...
Continue Reading
Stay safe from cybercrime with these five tips
Cybercriminals will use every tactic in the book to steal data, drain bank accounts, and extort ...
Continue Reading
Top 5 Security Considerations for a New Web App: 2. Authentication & Authorization
Welcome to my comprehensive series on the Top 5 Security Considerations for a New Web App. This ...
Continue Reading
Top 5 Security Considerations for a New Web App: 1. Secure Coding
Welcome to my comprehensive series on the Top 5 Security Considerations for a New Web App. For this ...
Continue Reading
Has contents: true
Total pages: 3
Current page: 1





.png)
.png)

