Frequently Asked Questions
Get the answers you need to choose the right security services for your organization.
How Secure Ideas partners with government contractors
Secure Ideas is an industry leading cybersecurity company that provides a range of security testing ...
Continue Reading
How often should web penetration testing be conducted?
Web application penetration testing is an essential part of keeping your web or mobile application ...
Continue Reading
What Risks Does the DarkWeb Pose to Businesses?
You have likely heard that the dark web (which is different from the "deep web") is often ...
Continue Reading
What Can I Expect During the Physical Penetration Testing Process?
A physical penetration test of your organization's physical location can be a valuable and ...
Continue Reading
Why Would I Need a Physical Penetration Test?
A physical penetration test is an attack on a company's physical security controls. As a business ...
Continue Reading
What is a Physical Penetration Test?
If you are wondering what a physical penetration test is, and what different types we offer, you ...
Continue Reading
4 Steps to prepare your application for a Denial of Service attack
When you hear the words "cyber attack," the first thing that comes to mind is probably ransomware ...
Continue Reading
What Tasks are Performed During a Hardware Security Assessment?
A hardware security assessment is a review of a physical device and a very common task when ...
Continue Reading
How is Embedded/IoT Scoping Different from a Normal Pentest?
consulting |
security |
penetration testing |
business |
scope |
IoT |
Embedded Device
A Penetration Test is a Penetration Test, Right? On the surface, that would be the case if we are ...
Continue Reading
Penetration Testing Compliance under GLBA in 2024 - What You Need to Know
information security |
penetration testing |
compliance |
risk assessment |
information security program |
GLBA |
Safeguards Rule |
vulnerability assessment
The Gramm-Leach-Bliley Act (GLBA) has established baseline privacy and cybersecurity standards for ...
Continue Reading
How Soon Can We Schedule a Test?
The short and sweet answer is that once a contract has been executed by both parties, and all ...
Continue Reading
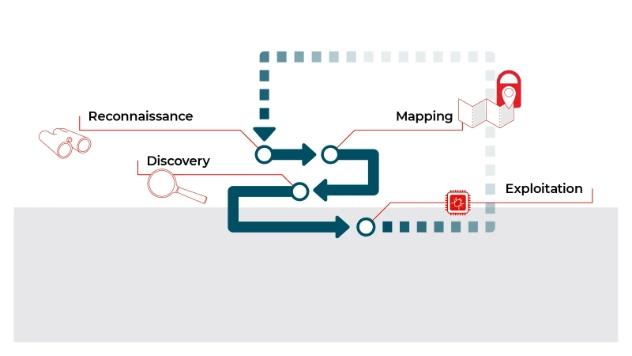
Secure Ideas' Penetration Testing Methodology
When it comes to partnering with an outside security consulting firm, there are many things to ...
Continue Reading
Has contents: true
Total pages: 8
Current page: 4



)%20(Blog%20Graphic)%20(1).webp)