Frequently Asked Questions
Get the answers you need to choose the right security services for your organization.
What factors impact the cost of a web application penetration test?
The complexity of the application primarily determines the effort to perform a web application ...
Continue Reading
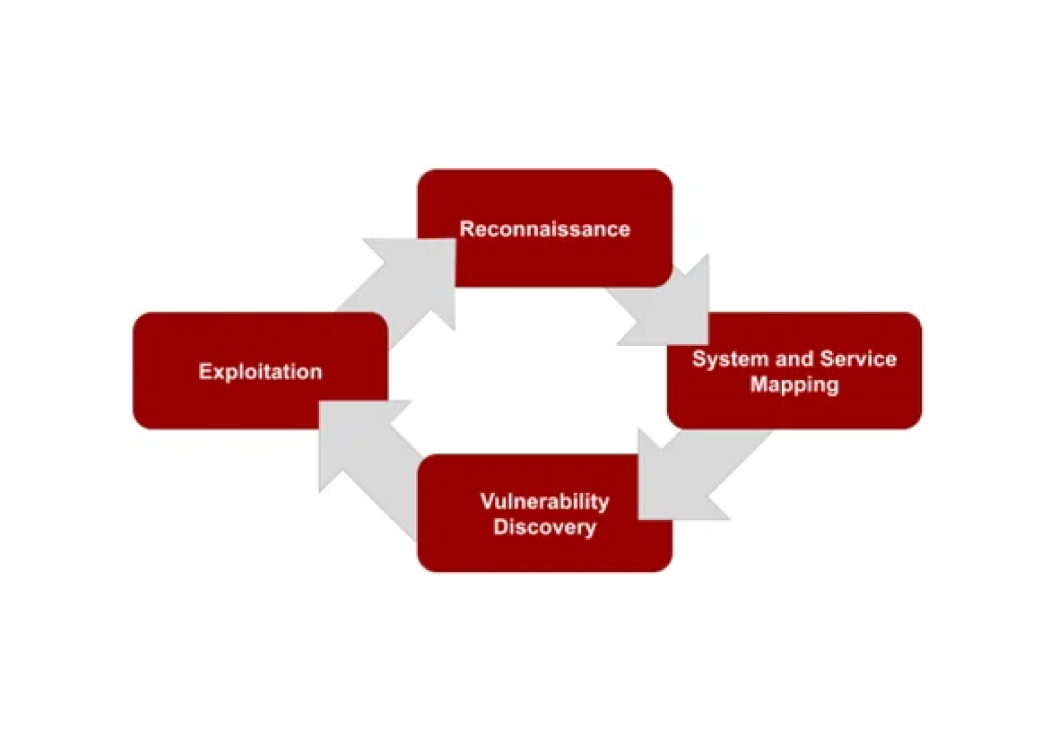
What is your penetration testing methodology?
Secure Ideas follows an industry standard methodology for testing the security of network ...
Continue Reading
What factors impact the cost of a mobile application penetration test?
The penetration testing of applications on a mobile platform comes with some challenges. Today's ...
Continue Reading
What factors impact the cost of an internal penetration test?
The effort to perform an internal penetration test can vary depending on several factors. Here are ...
Continue Reading
What factors impact the cost of an API or microservice penetration test?
FAQ |
penetration testing |
API |
cost
API or microservice penetration testing is different from other application penetration testing ...
Continue Reading
The Difference Between a Vulnerability Scan and a Penetration Test: Why It Matters for Compliance
If you have spent any time working through a compliance framework, you have probably noticed that ...
Continue Reading
What factors impact the cost of an external penetration test?
The basic structure of an external penetration test is to assess the external attack surface of ...
Continue Reading
What factors impact the cost of Reporting?
Our standard penetration test report follows a proven formula that includes:
Continue Reading
What is GLBA Compliance Penetration Testing?
When it comes to safeguarding student data, educational institutions must meet several compliance ...
Continue Reading
What is the Secure Ideas engagement process?
Engaging any company in penetration testing necessitates quite a bit of contract language. The good ...
Continue Reading
What are the Tools and Rules of Engagement at Secure Ideas for Web Application Penetration Tests?
Tools Utilized At Secure Ideas, we primarily leverage manual pentesting methodologies augmented ...
Continue Reading
How to Get the Most Out of Your Penetration Test: A Guide to Preparation and Success
When it comes to penetration testing, preparation isn't just helpful—it's essential for success. ...
Continue Reading
Has contents: true
Total pages: 3
Current page: 1