Penetration testing is an important process used by organizations to assess the security of their IT systems. It involves simulating an attack on a system to identify vulnerabilities and potential risks. There are different types of penetration testing, each of which targets a specific aspect of a system. In this article, we will discuss some common types of penetration testing.
Network Penetration Testing
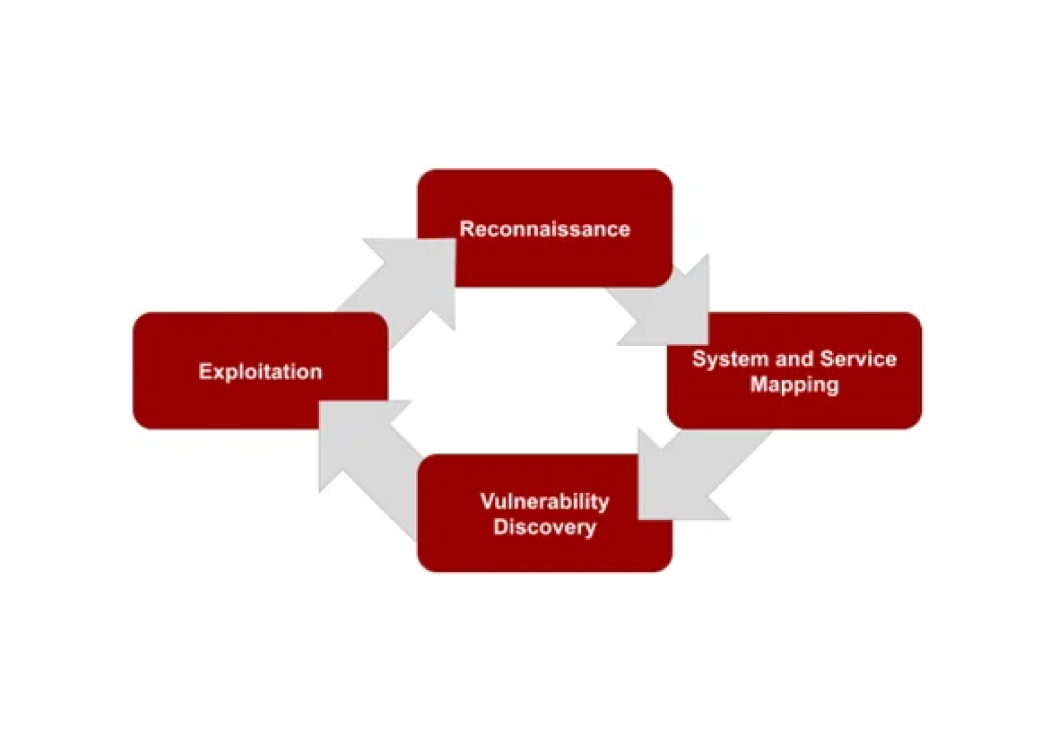
This type of testing focuses on identifying security vulnerabilities in the network infrastructure of an organization. Network penetration testing involves testing the security of firewalls, routers, switches, and other network devices. It also involves analyzing exposed services and may include other aspects such as leveraging protocol vulnerabilities, man-in-the-middle attacks, and cracking passwords. Network penetration testing is typically either from the perspective of an outside attacker (i.e. external test) or from the perspective of a compromised device inside the network (i.e. internal test). The goal of this testing is to identify potential vulnerabilities that could be exploited by an attacker to gain unauthorized access to the network, data, or functionality. See our network penetration testing service page for more details.
Application Penetration Testing
This type of testing focuses on assessing the security of web applications, mobile applications, APIs, and desktop applications. Application penetration testing involves interacting with the application to find flaws that could compromise the underlying system, circumvent authentication or authorization, or expose sensitive data. Application penetration testing may also include testing the security of the application's code, configuration files, and third-party integrations. The goal of this testing is to identify potential vulnerabilities that could be exploited by an attacker to gain unauthorized access to the application or its data. See our application penetration testing service page for more details.
Physical Penetration Testing
This type of testing involves attempting to gain unauthorized access to an organization's physical premises. Physical penetration testing involves testing the security of doors, windows, locks, and other physical security measures. It may also involve social engineering or evading detection. The goal of this testing is to identify potential vulnerabilities that could be exploited by an attacker to gain physical access to the organization's premises or to a sensitive area such as a data center. See our physical penetration testing service page for more details.
IoT and Embedded Device Testing
This type of testing focuses on identifying vulnerabilities and weaknesses in devices such as smart home devices, industrial control systems, and other internet-connected devices. IoT and embedded device testing requires specialized knowledge and tools to simulate attacks and assess the security of these devices. Aspects of these devices that may be considered during a penetration test include the firmware, network interfaces, access controls, physical interfaces, cloud connectivity, and wireless communication such as Bluetooth or Zigbee. See our IoT and embedded device testing service page for more details.
The different types of penetration testing are designed to assess the security of various aspects of an organization's IT system. By conducting regular penetration testing, organizations can identify vulnerabilities and potential risks and take steps to mitigate them before they can be exploited by an attacker. It is essential for organizations to work with experienced penetration testing professionals who can provide accurate and reliable testing results.
Want to know more about penetration testing? Check out our What is Penetration Testing page for all things pentesting.
Not sure which type of test you need?
Our team can help you determine the right type of penetration test for your organization's goals. Reach out to start the conversation.
Talk to Our Team