Penetration testing is an essential process that organizations use to identify potential security vulnerabilities in their computer networks, systems, applications, devices, and facilities. It involves simulating a real-world cyberattack to discover weaknesses in an organization's network, software, and hardware systems. However, it is important to remember that penetration testing is not a one-size-fits-all solution, and there are ethical and legal considerations that organizations must be aware of before embarking on such an exercise.
Ethical Considerations
Penetration testing can have ethical implications, and it is important for organizations to consider the following:
- Authorization: This refers to the need for explicit permission from the organization or individual who owns the system or network being tested. Without proper authorization, a penetration tester is effectively engaging in unauthorized access. Therefore, obtaining authorization is a crucial step to ensure that penetration testing is conducted ethically and legally. Clear documentation of the testing scope is essential to avoid misunderstandings and ensure that the testing is conducted in a controlled and ethical manner.
- Transparency: Penetration testers must be transparent to their clients about their methodology, tools, and techniques. This means that they should not keep any aspect of their testing methodology a secret and must fully disclose their methods to their clients. This transparency is necessary to ensure that clients understand how the testing is being conducted and can provide feedback if necessary. By being open about their testing process, testers can also build trust with their clients, who will have a better understanding of the work being done and the potential implications of the results.
- Confidentiality: Organizations and penetration testers must ensure that the data collected during the penetration testing exercise is kept confidential and not shared with unauthorized parties. This includes the use of secure data storage and destruction methods. Additionally, testers have a responsibility to maintain the confidentiality of their findings. They should not publicly disclose any information about a vulnerability that could lead to an attack against the client. Instead, they should only share the findings with authorized personnel and ensure that the information is protected from unauthorized access. Testers must balance the need to disclose vulnerabilities with the need to maintain the security of their clients. This requires careful consideration and collaboration with the client to determine the appropriate level of disclosure and the best way to remediate any vulnerabilities that are discovered.
- Responsibility: Organizations must ensure that their penetration testing exercise is conducted in a responsible and professional manner, and that no harm is caused to their employees, customers, or stakeholders during the process. This includes implementing appropriate safeguards to prevent damage to systems or networks and ensuring that the testing does not disrupt critical business operations. In addition, organizations must take responsibility for addressing any vulnerabilities discovered during the penetration testing exercise promptly. This includes prioritizing and addressing the vulnerabilities in a timely and effective manner to minimize the risk of exploitation.
Legal Considerations
Penetration testing can also have legal implications, and it is important for organizations to consider the following:
- Compliance: Organizations must ensure that their penetration testing exercise complies with all applicable laws and regulations, including data protection laws, privacy laws, and intellectual property laws. For example, in the United States, organizations must comply with the Computer Fraud and Abuse Act (CFAA), which criminalizes unauthorized access to protected computers. Additionally, the Electronic Communications Privacy Act (ECPA) regulates the interception and disclosure of electronic communications, and the General Data Protection Regulation (GDPR) in the European Union provides strict requirements for the processing and protection of personal data.
- Liability: Organizations must consider the potential liability that may arise from the penetration testing exercise, including any damage caused to the network or systems as a result of the testing, or real-world implications that might be tied to those systems. This may include both civil and criminal liabilities, depending on the nature and severity of the damage caused. To mitigate this liability, organizations must ensure that they engage qualified and trustworthy penetration testers who have the necessary skills and experience to conduct the testing. This includes verifying the credentials and track record of the testers, as well as ensuring that they follow strict ethical standards and best practices in their work. Additionally, organizations should ensure that they have appropriate insurance coverage to protect against potential liability arising from the penetration testing exercise.
- Documentation: Organizations must maintain detailed records of their penetration testing exercise, including the scope of the test, the methods used, and the results obtained. This documentation is essential to demonstrate that the organization has acted in a responsible and professional manner during the testing process and to comply with regulatory and legal requirements. Furthermore, maintaining detailed records of the penetration testing exercise can help organizations to demonstrate due diligence in the event of a security breach. By providing evidence that they have taken reasonable steps to protect their systems and networks, organizations can reduce their potential liability and minimize the impact of a breach.
In conclusion, penetration testing is a critical process for identifying potential security vulnerabilities in an organization's computer systems. However, it is important for organizations to consider the ethical and legal considerations before embarking on such an exercise. By doing so, organizations can ensure that their penetration testing exercise is conducted in a responsible and professional manner, and that the potential risks are mitigated.
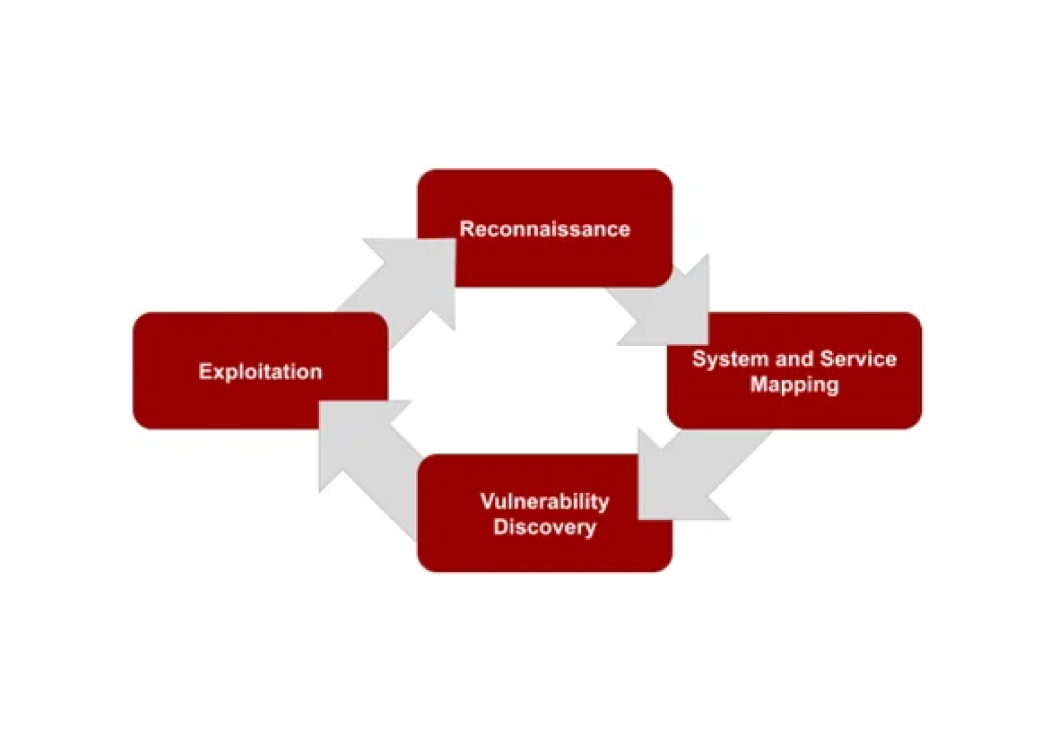
Wondering what the actual process looks like?
Authorization, scoping, documentation: we handle all of it. See how a professionally run engagement works from start to finish.
See Our Engagement Process