Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Houston, We Have a Problem
Satellite Security Testing: A Holistic Approach Last month, I had the opportunity to present at ...
Continue Reading
Cybersecurity Essentials for SMBs: Building a Robust Program
When discussions arise around companies' cybersecurity programs, the focus often gravitates towards ...
Continue Reading
The Essential Eight
NIST |
Essential 8 |
ASD
Australian Signals Directorate's Top 8 Controls to Mitigate Cybersecurity Incidents and How They ...
Continue Reading
From Nmap to CSV
How Experience and Management Skills Improve Data Analysis for Security Professionals The other ...
Continue Reading
You Don’t Need PKINIT To Win It
Privilege Escalation using LDAP Part 1 Pass-the-certificate has become a common method used by ...
Continue Reading
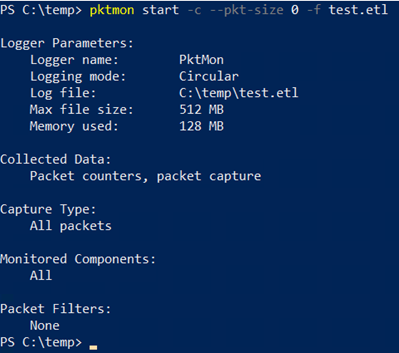
Built-In Network Capture with Windows 11
Did you know that Windows has a built-in network packet capture utility? And that it isn't even GUI ...
Continue Reading
Running and Debugging Non-native ELF Binaries Locally Using QEMU, BINFMT, and GDB
One of the common tasks that occurs when pentesting an embedded device is binary analysis of ...
Continue Reading
Who Really Owns Your Data?
When we traded ownership for convenience, we never imagined that everything from our books to our ...
Continue Reading
When Algorithms Aren’t Enough: Why the Human Element Still Matters in Modern Penetration Testing
The cybersecurity industry has evolved into two distinct approaches when it comes to penetration ...
Continue Reading
OT: The Invisible World in Motion
We are surrounded by technology, not just in what we carry but in nearly every aspect of our daily ...
Continue Reading
Solicited Public Comment on HIPAA Security Rule NPRM To Strengthen the Cybersecurity of ePHI
The Department of Health and Human Services (HHS) wants to raise the benchmarks of the Security ...
Continue Reading
Has contents: true
Total pages: 33
Current page: 4

.png)