Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Policy Gap Analysis: Filling the Gaps
In today’s world, something never seems to be true unless it is written down, and even then it is a ...
Continue Reading
New Data Security Breach Laws in Florida
Since many organizations are collecting what many would consider personal, non-public, information, ...
Continue Reading
What Do You Expect From A PenTest?
There are many reasons that a company has a penetration test performed. Maybe it is due to ...
Continue Reading
Comprehensive Testing: Red and Blue Make Purple Video
James Jardine and I held the Comprehensive Testing (Purple Teaming) webcast yesterday. In this ...
Continue Reading
Purple Teaming for Success
You know what blue teams and red teams are. Red is our attack side, or the adversaries, and Blue is ...
Continue Reading
Oversharing: Who Has Access?
What types of information do you copy to a shared folder? Who has access to the share? This can be ...
Continue Reading
Is My Application Illegal?
Mobile devices and applications are everywhere. And we have seen tons of information, guides and ...
Continue Reading
Decoding Security Jargon
If you pick up just about any security textbook it will begin by describing security using terms ...
Continue Reading
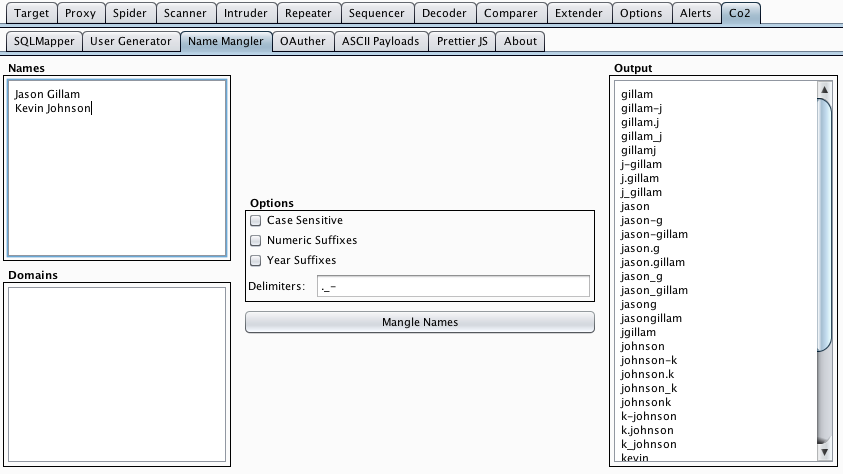
Burp Co2 Update v0.5 adds a Name Mangler module!
I’m excited to announce another addition to the Burp Co2 extension bundle in v0.5 of Burp Co2 ...
Continue Reading
Are we a Target?
2014 has started out with a bang in terms of publicly disclosed compromised systems. We entered the ...
Continue Reading
Scary Web Services: Part 2
This post may seem timely in light of the recent Snapchat compromise. Although Snapchat’s breach ...
Continue Reading
Has contents: true
Total pages: 33
Current page: 27