This week I’ve been teaching a class on web app security for developers and I remembered a fun little script that I thought I’d share here. That script is BozoCrack, written by Juuso Salonen. I’d give my description of what this tool does, but I’ll use Juuso’s words from his GitHub page instead. It’s pretty classic.
BozoCrack is a depressingly effective MD5 password hash cracker with almost zero CPU/GPU load. Instead of rainbow tables, dictionaries, or brute force, BozoCrack simply finds the plaintext password. Specifically, it googles the MD5 hash and hopes the plaintext appears somewhere on the first page of results.
It works way better than it ever should.
Download here: https://github.com/juuso/BozoCrack
I can tell you that this really is the case. I’ve dumped MD5 hashes from apps, tossed them at BozoCrack, and got the original passwords back in just a few seconds. It doesn’t work in all cases of course, since Google has to see the MD5 hash some where and have the original text on the same page as the hash. The script is written in Ruby and doesn’t need any particular modules installed on it.
Here is an example of five MD5 hashes that I dumped from a vulnerable web app installed on SamuraiWTF.
5f4dcc3b5aa765d61d8327deb882cf99
e99a18c428cb38d5f260853678922e03
8d3533d75ae2c3966d7e0d4fcc69216b
0d107d09f5bbe40cade3de5c71e9e9b7
5f4dcc3b5aa765d61d8327deb882cf99
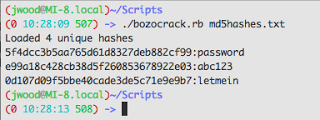
Note that the first and last hashes are identical. When I turn BozoCrack loose on them, we get the following results.
The time stamp in my command prompt tells the tale on how fast this ran. We got 3 out of 4 passwords back from BozoCrack and it took 4 seconds to do so. “Depressingly effective” indeed!
The defense for this is actually pretty simple. Whether or not we can do the same search for MD5, SHA1 or SHA256 hashes, just add a salt to your password hashing function. Then the chances of finding the original text via a Google search starts going down rapidly. Here’s a pretty good write up on using salts with your password hashes. http://crackstation.net/hashing-security.htm
Happy Hacking!
Jason Wood is a Senior Security Consultant at Secure Ideas. If you are in need of a penetration test or other security consulting services you can contact him at jason@secureideas.com or visit the Secure Ideas – Professionally Evil site for services provided.