In this series of the Professionally Evil Toolkit we will be talking about sqlmap. Sqlmap is an open source penetration testing tool that is written in Python. Sqlmap automates the process of detecting/exploiting SQL injection flaws and taking over database servers. As you might know, SQL injection is ranked number one on the OWASP Top Ten of web application security vulnerabilities. Since sqlmap has a rich feature set full of options, we will be covering an introduction to the tool.
First you should have sqlmap downloaded and installed on your machine used for testing. If you don't want to install it, SamuraiWTF and Kali Linux come with this preloaded.
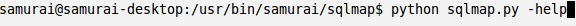
To launch sqlmap in Samurai we will just open up a shell, browse to the /usr/bin/samurai/sqlmap directory, and type in python sqlmap.py. However, sqlmap requires parameters to run. We can issue the --help command to get help on the tool. Below is a screenshot of the command:
We are going to cover the basic functionality of the tool next. This can be broken up into several parameter categories: Target, Request, Injection, and Enumeration.
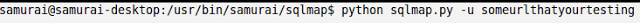
The target parameter is a requirement as it specifies which URL for sqlmap to test against. An example of this would be:
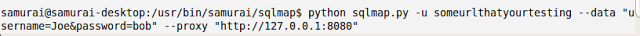
The next parameter category is the request parameter. Below are some useful request parameters with descriptions:
- Data: The ability to put a data string in a request to make it a POST request
- Cookie: Set a cookie for the request
- Random-Agent: Randomizes user-agent header value
- Force-ssl: Very useful on sites that are SSL based
- Proxy: Great for troubleshooting. Instructs sqlmap to use a proxy (Burp works great)
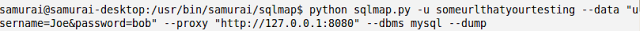
Below is an example of running sqlmap on a login screen using a POST request with a local client side proxy:
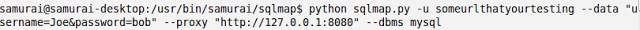
The next parameter category is the injection parameter. This parameter allows you to specify the back end DBMS if you know it, and to specify a parameter. By default, if no parameter is specified, sqlmap will try all parameters. We will build on the above example and specify a MySQL backend:
Finally, the last parameter category field we are going to talk about is enumeration. Enumeration gives you the ability to grab banners, current users, current database, passwords, tables, columns, schemas, and even allows the full database dump. Using the example above we can enumerate and dump the entire database using the following command:
To learn more about sqlmap you can use the help page or find more information at sqlmap.org. If you're looking for something to test against in a sandboxed environment you could try Mutillidae.
Want a team that goes beyond automated scanning to find SQL injection?
Our consultants use tools like sqlmap alongside manual testing techniques to find injection flaws that scanners miss. Reach out to discuss a web application penetration test.
Talk to Our Team