Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Ransomware Intelligence Briefing
Ransomware Intelligence Briefing Media reporting on the WannaCry ransomware campaign has contained ...
Continue Reading
Protecting your Kids from Online Threats
“The greatest gifts you can give your children are the roots of responsibility and the wings of ...
Continue Reading
An Introduction to Javascript for XSS Payloads
I recently got the opportunity to speak at B-Sides Charleston on cross-site scripting (XSS) payload ...
Continue Reading
A Brief BeEF Overview
BeEF, the Browser Exploitation Framework, is a testing tool that allows the penetration tester to ...
Continue Reading
SQLMap Beginnings: What and How
Testing web based applications is not only fun but is often multi-faceted and challenging. Often ...
Continue Reading
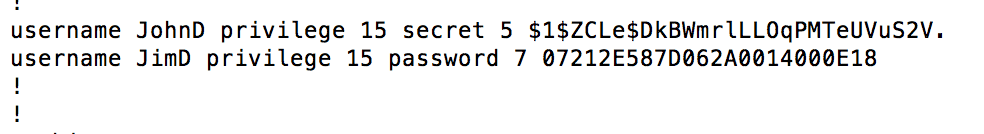
Reversing Type 7 Cisco Passwords
While working on a recent pen test, I came across a few Cisco routers sitting on an internal ...
Continue Reading
We're Just Like the NSA, and Nothing Like Them
During penetration tests, and especially scoping calls, we often get quizzed about what secret, ...
Continue Reading
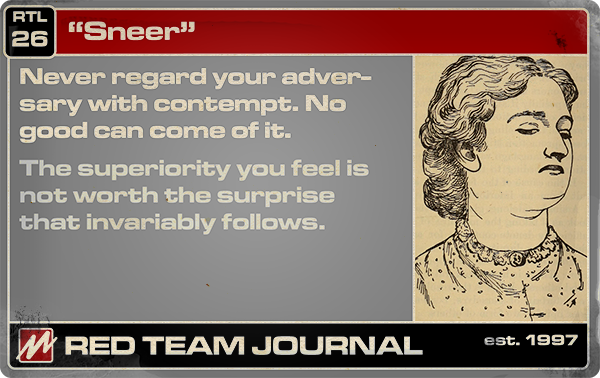
Red Teaming - Not What You May Have Thought
Lately, I’ve been doing a lot of reading on some less technical topics and I ran across “Red Team: ...
Continue Reading
Five Outdated Security Excuses
The Security Industry as a whole has been known to criticize businesses large and small with ...
Continue Reading
Introduction to Metasploit Video
The Metasploit Framework is a key resource for security assessors. Whether you’re goal is to become ...
Continue Reading
Introducing Burp Correlator!
This one is for you web penetration testers! This new Burp extension is designed to help with ...
Continue Reading
Has contents: true
Total pages: 33
Current page: 25



.webp)