Professionally Evil Insights
Welcome to the Professionally Evil Insights blog by Secure Ideas! In this digital playground, we unravel the complex world of information security with a touch of fun. Our expert-led content ranges from deep-dives into penetration testing to explorations of hardware hacking. Whether you're curious about Secure Ideas or passionate about cybersecurity, this blog is your quick, enlightening, and entertaining guide into the captivating world of information security.
Welcome aboard!
Twelve Days of ZAPmas - Day 2 - The Edge of Tomorrow
Day 2 - The Edge of Tomorrow - Replaying and Tampering with Requests Fuzzing and tampering are like ...
Continue Reading
Twelve Days of ZAPmas - Day 1 - Setting Up ZAP
This holiday season, I’m going to run down some of the ins and outs of working with OWASP Zed ...
Continue Reading
Coming Soon - Twelve Days of ZAPmas
In December of 2018, I published a twelve-day series of cross-site scripting tips, tricks, and ...
Continue Reading
Three Excellent API Security Practices Most People Neglect
We are very much in the age of APIs. From widely-used single-purpose products like Slack to ...
Continue Reading
The Death and Rebirth of Musashi.js OR How I turned personal failure into better teaching tools.
A little background… As I stood in front of a class of developers trying to explain cross-origin ...
Continue Reading
Waving the White Flag: Why InfoSec should stop caring about HTTPOnly
As a company that is constantly working with our penetration testing clients on understanding where ...
Continue Reading
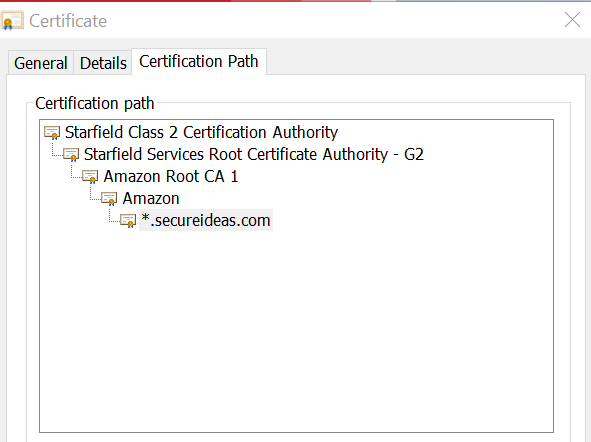
Proxying HTTPS Traffic with Burp Suite
The Problem For newcomers to application penetration testing, a reasonably common question is How ...
Continue Reading
Getting Started API Penetration Testing with Insomnia
In our blog series on Better API Penetration Testing with Postman we discussed using Postman as the ...
Continue Reading
Better API Penetration Testing with Postman – Part 4
This is the final part of this series on putting together a better API testing tool-chain. In Part ...
Continue Reading
Better API Penetration Testing with Postman – Part 3
In Part 1 of this series, we got started with Postman and generally creating collections and ...
Continue Reading
Better API Penetration Testing with Postman – Part 2
In Part 1 of this series, I walked through an introduction to Postman, a popular tool for API ...
Continue Reading
Has contents: true
Total pages: 4
Current page: 3