If you have spent any time working through a compliance framework, you have probably noticed that the requirements around security testing can feel a little vague. Terms like vulnerability assessment, penetration test, and security scan can sometimes appear without much explanation, and in some cases get used interchangeably, even though they describe very different activities. That distinction matters, both for understanding what you are actually getting and for demonstrating that you have met your compliance obligations.
What a Vulnerability Scan Actually Does
A vulnerability scan is an automated process where a tool reaches out to systems on your network, checks what it finds against a database of known vulnerabilities, and then produces a report. It is fast, repeatable, and useful for getting a broad picture in regard to known weaknesses across your environment. Most scanners will flag things like outdated software versions, missing patches, default configurations, and open ports that probably should not be open.
What a scan does not do is tell you whether any of those findings are actually exploitable in your environment. A scanner might flag a potentially vulnerable service and assign it a high severity rating, but that rating comes from the generic characteristics of the vulnerability, not from any attempt to use it against your specific system. The scan identifies candidates for concern. It does not confirm that a real attacker could do anything with them.
What a Penetration Test Is Designed to Do
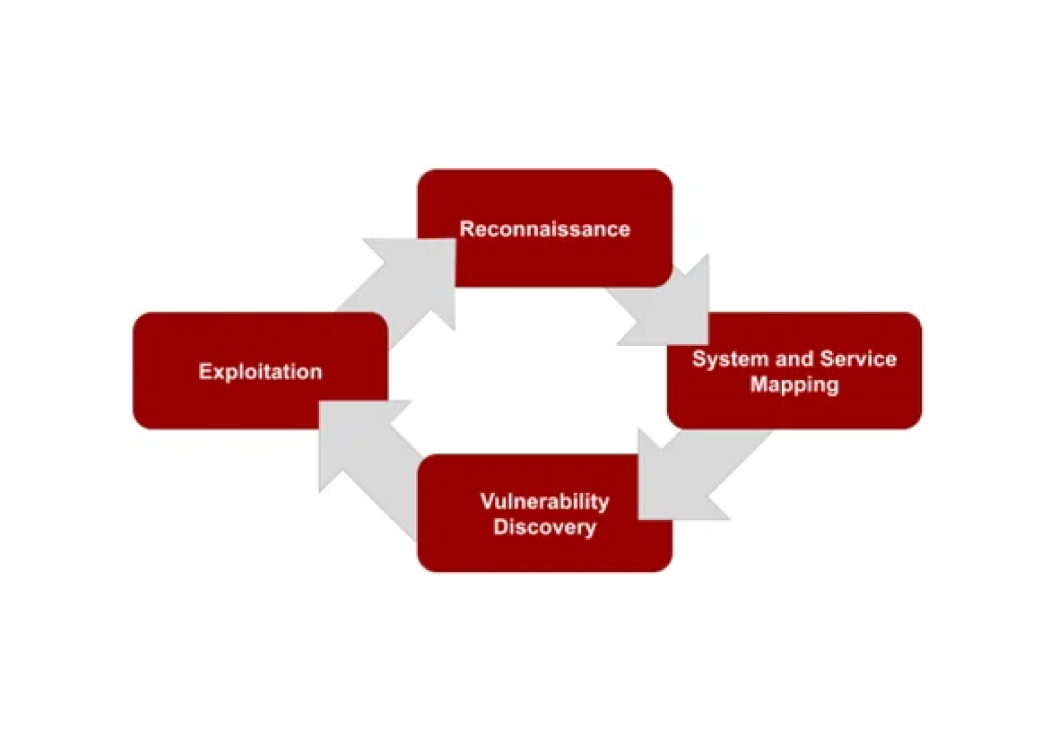
A penetration test approaches your environment the way an attacker would, starting not from a checklist but from an objective: find a way in, and determine how far that access goes. A tester, a person and not just a tool, independently evaluates the environment using a combination of their own reconnaissance, any available scan data, and judgment that comes from experience. That means trying to exploit vulnerabilities, chain together multiple weaknesses, and probe the logic of how systems are designed and implemented.
A skilled tester reads the environment where a scanner only catalogs it, recognizing when something that looks low-risk in isolation becomes significant in context. Misconfigurations, logic flaws, and unexpected combinations of otherwise minor issues tend to show up in penetration tests and nowhere else.
The result is something a scan report cannot produce on its own: a narrative account of real risk grounded in what an attacker could actually do in your specific environment. That distinction between a list of potential vulnerabilities and a validated picture of actual exposure is precisely what compliance frameworks are asking for when they require a penetration test.
Why the Difference Matters for Compliance
Most compliance frameworks that require security testing are not just checking a box. They are trying to verify that you have a realistic understanding of your actual risk. When a framework specifies a penetration test, a vulnerability scan is not an equivalent substitute, even if the scan report looks impressive.
This comes up regularly with frameworks like PCI DSS, which explicitly differentiates between vulnerability scans, required regularly from both internal and external perspectives, and penetration testing, required at least annually and after significant changes to the environment. HIPAA's Security Rule requires covered entities to conduct a thorough risk analysis, which is difficult to demonstrate with scan output alone. The GLBA Safeguards Rule, with requirements that took effect in 2023, gives covered organizations two options for meeting their monitoring requirements: either implement continuous monitoring or conduct annual penetration testing combined with vulnerability scans at least every six months. A scan alone satisfies neither path.
Using a scan to satisfy a penetration testing requirement puts you in a position where you may believe you are compliant when you are not. That gap tends to surface at the worst possible time: during an audit, after an incident, or when a regulator asks for documentation.
A Practical Way to Think About It
If you want a quick mental model, a vulnerability scan tells you where the doors and windows are, and whether any of them look like they might be unlocked. A penetration test tells you which ones actually open, what is on the other side, and how far in someone could get before they hit the next obstacle.
Both have a place in a security program. Scans are cost-effective for ongoing monitoring and keeping a current picture of your environment. Penetration tests give you the validated, narrative-driven evidence that compliance frameworks are actually looking for, along with the kind of findings that hold up when someone with authority asks whether you really know your risks.
If you are unsure which one your compliance requirement is actually asking for, the answer is almost always in the specific language of the standard. When it says penetration test, it means penetration test.
Need a penetration test that satisfies your compliance requirements?
Whether you are working toward PCI DSS, HIPAA, GLBA, or another framework, our team delivers the validated, narrative-driven results that auditors and regulators are looking for. Reach out to discuss your testing needs.
Talk to Our Team