Web applications are now remarkably complex. Whether its Internet of Things (IoT) devices, mobile apps, desktop client applications, or web applications native to the browser, programming language frameworks, or cloud services, all of these types of software are powered by an API (Application Programming Interface). In simple terms, an API is a list of interactions between two or more pieces of software. APIs describe how the parties can communicate, what kinds of function calls or requests can be made, how to make them, the data formats, and what conventions to follow.
APIs are immensely powerful. Most modern applications are built of a series of calls to multiple APIs. When we test a web application, we cover the API calls made by the application. However, if the web application only covers a small portion of the API then a lot of that functionality is unexamined.
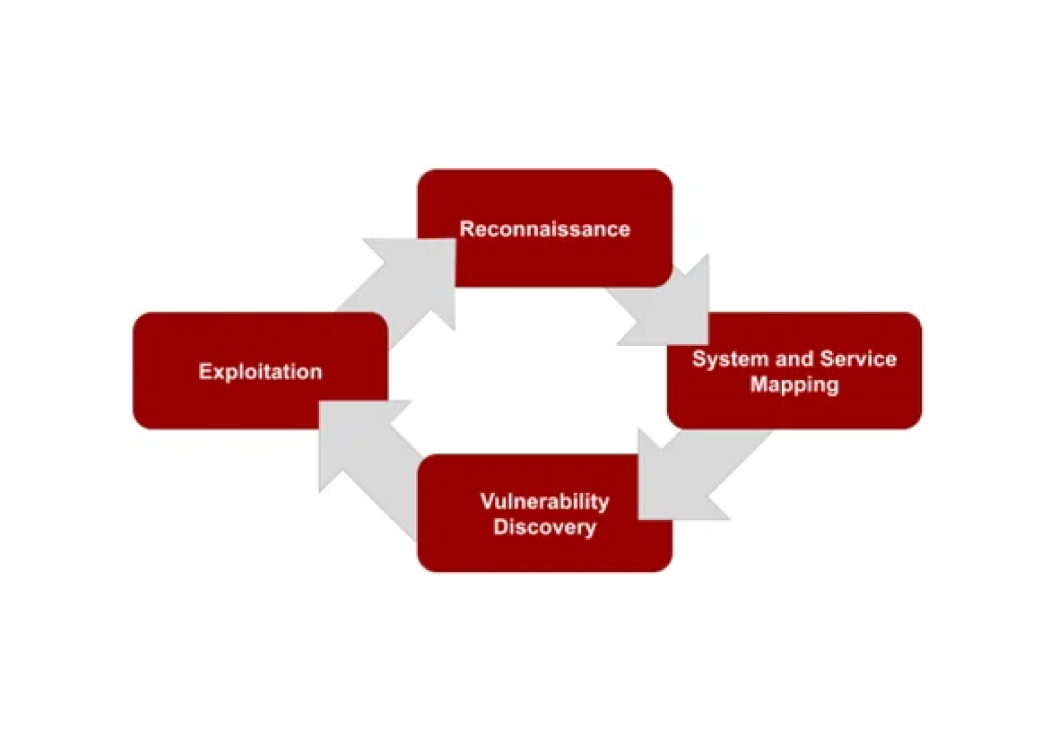
An API penetration test focuses on the backend logic of the servers themselves. We analyze the HTTP requests and the data that flows between requests and responses. On an API pentest, we don't focus as much on vulnerabilities that can manipulate or exploit browser behavior. Instead, the focus is on the authorization and authentication mechanisms that the application is built on. There may be vulnerabilities hidden within the functionality of an API that aren't easily accessible through a web application. The OWASP Top 10 API Security Project is a good reference for the most critical flaws within an API.
If your organization relies on internal or third-party APIs for your web applications you should get your penetration test done by a company that knows how to test APIs. If you're interested in learning how to conduct this type of assessment, we have tutorials on how to do a pentest with both Postman and Insomnia.
Need your API tested?
Our team tests REST APIs, GraphQL endpoints, SOAP services, and more. Reach out to discuss scoping a test for your API.
Talk to Our Team