There are several ways to pull firewall information from a Windows system. Today we will leverage Powershell to quickly find and review the different Remote Desktop rules that are in place. This use case revolves around Remote Desktop being our key search term, but this filter can be adjusted to fit whichever rule you’re looking for. A quick example can be found in the command block below:
| $a = netsh advfirewall firewall show rule name=all | Select-String -Pattern "Rule Name:\s+Remote Desktop" | %{ ($_ -split ":")[-1].Trim() } |
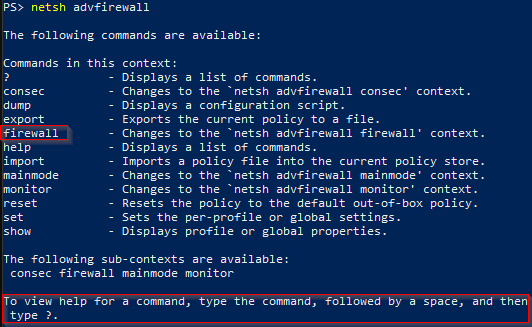
The variable ($a) is used to store the results of the netsh advfirewall command. If you just type in the first part of the command by itself (netsh advfirewall), then you’ll see that a list of additional command options are available for you.

The next option we’re going to add is the firewall command. A question mark (?) can be used to get more information on a particular command. This is an easy way to build a command while looking through the options at each step and determining how you want to construct your query. After you’ve tacked on the next couple options, you should see some usage and example information, similar to this:

You should also notice that one of the built-in examples provided is a rule name that is equal to all, which is what we’re looking for. The second section of the command (Select-String -Pattern "Rule Name:\s+Remote Desktop") is simply doing a pattern search for any rules that match on Remote Desktop. Whereas the last portion of the command ( %{ ($_ -split ":")[-1].Trim() } ) is meant to clean up and trim the empty space between the field name and the rule name.
From here, you’ll want to test your output to make sure that everything looks correct. This can be done by using the foreach loop below, or simply typing out the variable ($a). Also, it’s worth noting that any variables created this way are temporary and will be lost when the powershell window closes.
Next, we’re going to take all of the rule names discovered, and iterate through each one. The rule name will get stored in the ($i) variable.
Depending on the device this is being run against, you may get a list of several RDP rules and their settings. If you’ve got access to view the information then you should see if the Remote Desktop rules are present, enabled, or specific to a particular firewall profile. They can range from the basic or default rules governing inbound TCP traffic, to User Mode for either TCP or UDP protocols. It may also include a Shadow entry, which allows administrators to remotely view and interact with the user’s desktop environment.

While this article mainly focused on advfirewall, there’s more than one way to extract this type of information. For example, the command below can also pull similar firewall information by using the Powershell Get-NetFirewallRule cmdlet, and then applying a description filter to only search for matches on remote desktop.
Additionally, if you’re interested in security fundamentals, we have a Professionally Evil Fundamentals YouTube channel that covers a variety of technology topics. Finally, if you’re looking for a penetration test, training for your organization, or just have general security questions please Contact Us.