A Penetration Test is a Penetration Test, Right?
On the surface, that would be the case if we are oversimplifying things. However, there are some things to consider when you need to get your new embedded/IoT product tested. This article will outline some considerations to think about when you are setting up your test and understanding your threat models.
Fully Enumerate the Attack Surfaces
Embedded/IoT devices rarely operate in a vacuum. Most of these solutions contain more than one moving part that may need to be tested, such as the examples below:
- Services on device
- Services in the cloud
- Desktop/mobile applications
- Firmware/file system
- Physical hardware
- Networking
- RF and signal usage
- Privacy and compliance concerns
The list above isn't comprehensive, nor will it apply to every device, but does provide some things to consider. Your solution might have all of these or a mix of them. But fully understanding your attack surface can go a long way to correctly scoping your penetration test.
Understand the Ecosystem and Deployment
When preparing for a penetration test of an embedded/IoT device, it's also important to take some time to consider not just the device itself, but the full ecosystem of the solution.
- What are the attack surfaces of each part?
- What parts of the ecosystem can talk with each other?
- Who manages and deploys each part of the ecosystem?
- Is there any implicit trust of data in this system?
- How are you handling updates for all these components?
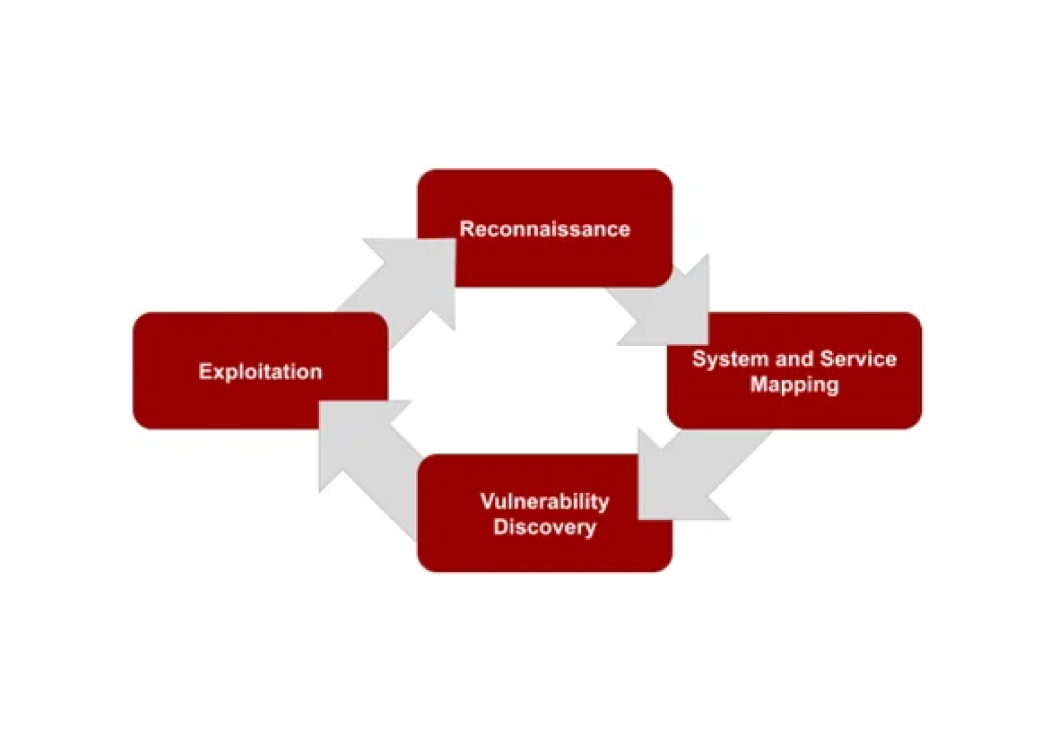
The list above again isn't comprehensive, but gets you started on what to consider. Once you have a better understanding of your complete attack surface, it will be easier to consider what parts need to be tested and how best to conduct testing your embedded/IoT solution.
Need your embedded or IoT device tested?
Our team tests the full ecosystem: hardware, firmware, cloud services, mobile apps, and everything in between. Reach out to discuss scoping a test for your device.
Talk to Our Team