Testing web-based applications is not only fun but is often multi-faceted and challenging. Often a web front end will have places for data input. Those that do, often store this information into some sort of back-end or database. The architecture will often be on a separate, dedicated purpose-built host. This means that a connection from the web/application server (may be one or two separate hosts) must connect to the database in order to store or retrieve data. For firms that are data-centric in their business model, the data in the database may be some of the most sought after to unauthorized persons. This aspect of internet-facing web-based applications makes them a constant target. Not surprisingly, playing defense against the threat spectrum is a never-ending game.
For those of us who are interested in protecting such data we must think like the "bad guys." This is an odd paradigm and admittedly, a bit uncomfortable at first for many. But since our goals are to find vulnerabilities and help in closing them before criminals do, it becomes something we just do.
So when we encounter a situation where we suspect a database is being used, we want to be able to discover as much information as any nefarious person. This allows us to detect and understand what risk a vulnerability may expose our client to. In order to exploit any weakness, we first have to find it, and before we do that we need to fingerprint the technology as much as possible. This work can be tedious but rewarding.
Knowing what technologies are being used helps us narrow our focus. Is the application vulnerable to injection attacks? Can we bypass any security layers to obtain information from the database without using the correct credentials? The answer is, "it depends." Experience will help but even that alone is often insufficient. What we need is a means for determining as much about the database as we can possibly obtain without triggering alarms. Not surprisingly, we often use tools for such tasks.
One such tool is SQLMap. It was made for obtaining data about a targeted database, which particular type of database is in place, how it is laid out, and if the application using the database is vulnerable to injection-based attacks. SQLMap can perform such data gathering and more. It may also identify the operating system of the host where the database resides. For a web-based target, it needs only a URL as input initially. Depending on what one finds, additional switches and options can be used to delve deeper into the target system.
Where Do I Obtain It?
There are several places to obtain SQLMap. You may download it and set it up on your platform of choice from the SQLMap website. Since the tool is written in Python, that must be installed before this tool will function. No matter which platform you choose to use, ensure the version you select is the right one for the operating environment you wish to use.
SQLMap can be found pre-installed in the Samurai Web Testing Framework. Of course, we at Secure Ideas are a bit biased when it comes to SamuraiWTF. SQLMap also comes with Kali, the open source penetration testing distribution maintained and distributed by the team at Offensive Security.
Within SamuraiWTF, SQLMap is located in the Exploitation/SQL folder or you can open a terminal and change to the /opt/samurai/sqlmap directory or select from the GUI:

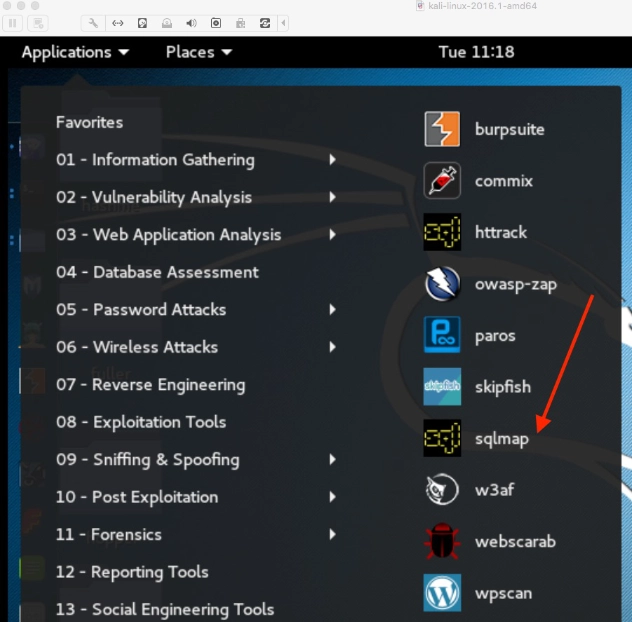
While we won't go into how to set up Kali or SamuraiWTF, within Kali you will find SQLMap under both the "Web Application Analysis" section as well as the "Database Assessment" section.
Getting Started
An alternative means of invoking SQLMap within Kali or SamuraiWTF is merely to type sqlmap from a command line. Provided that Python is installed and in the PATH of the user context from which it is being invoked, it will be available. If using this method without switches, it will display its usage syntax. For example:
$ python sqlmap
You will receive output that reminds you that the tool requires further parameters in order to operate:
samuraiwtf@samuraiwtf-Desktop:~$ sqlmap Usage: python sqlmap [options] sqlmap: error: missing a mandatory option (-d, -u, -l, -m, -r, -g, -c, -x, --wizard, --update, --purge-output or --dependencies), use -h for basic or -hh for advanced help
Note that there are several features that should be of particular interest in the output above. The two "help" switches -h and -hh are noteworthy because those will show basic help and advanced help respectively. The number of options are lengthy and will not all be covered here as they include options, target, requests, injection, detection, techniques, enumeration and other general information that we can use to pass to this tool.
However, the options that are listed after just invoking sqlmap show several switches that we can use to start using SQLMap.
If testing a web-based application known or suspected of using a database, the minimum needed is the -u switch. This parameter followed by the uniform resource locator (URL) enclosed by double quote marks. This combination tells SQLMap the target we want it to interact with. An example would be:
$ python sqlmap -u "http://www.secureideastraining.com/index.php?page=user-info.php"
In the above example the URL would be the target that you are authorized to test.
Now is a good time to mention that it is unethical and likely illegal to perform any sort of test of a site that you are not expressly given written permission to do so. If you have not already done so, look into setting up your own virtual lab environment. Consider running virtual hosting software and running your own hosts to attack. One such application is OWASP's Mutillidae 2 Project. There are plenty of vulnerabilities intentionally included in Mutillidae so that you can run SQLMap against it. You could also use the variety of vulnerable targets built into the SamuraiWTF project.
For those who have never used this tool or are new to SQL databases, you may wish to use the "wizard" switch. That is invoked by adding --wizard to the end of the string noted above. For example:
$ sqlmap -u "http://www.secureideastraining.com/index.php?page=user-info.php" --wizard
If used, you will be given several options to choose from regarding "injection difficulty level" and "Enumeration." The selections are simple 1-3 choices and look like this:
[18:45:26] [INFO] starting wizard interface POST data (--data) [Enter for None]: --data Injection difficulty (--level/--risk). Please choose: [1] Normal (default) [2] Medium [3] Hard > 1 Enumeration (--banner/--current-user/etc). Please choose: [1] Basic (default) [2] Intermediate [3] All > 3 sqlmap is running, please wait..
One of the cool features of SQLMap is that it provides feedback on what other parameters should be considered based on what it finds. For example, the output from the wizard selections above run against a Mutillidae instance resulted in the following:
[18:51:16] [CRITICAL] considerable lagging has been detected in connection response(s). Please use as high value for option '--time-sec' as possible (e.g. 10 or more) [19:41:12] [CRITICAL] all tested parameters appear to be not injectable. Try to increase '--level'/'--risk' values to perform more tests. Also, you can try to rerun by providing either a valid value for option '--string' (or '--regexp') If you suspect that there is some kind of protection mechanism involved (e.g. WAF) maybe you could retry with an option '--tamper' (e.g. '--tamper=space2comment')
Note the suggestion to increase the level and risk values as well as the --string or --regexp, and even the --tamper options. Use the basic and advanced help features to explore additional options. SQLMap offers a rich feature set and the security professional should be familiar with its capabilities so it is well worth the time spent in learning to use it.
Want a team that goes beyond automated scanning to find SQL injection?
Our consultants use tools like SQLMap alongside manual testing techniques to find injection flaws that scanners miss. Reach out to discuss a web application penetration test.
Talk to Our Team