One thing I notice a lot of people are missing in their skill set as security professionals is the ability to write NSE scripts for Nmap. This skill isn't too hard to learn and by not learning it, you are leaving a lot of value on the table. I feel like the issue though is that there isn't a lot of good content and examples to learn from other than the existing scripts out there and reading the Nmap book that covers this topic. I wanted to take a moment to write a series of blogs to cover what NSE is, what it can be used for, and provide a few examples of writing scripts. With the examples, I don't want to just cover the script, but the process to determine when to use NSE and the process of designing it from start to finish.
This blog will serve as the first entry here and cover a high-level overview of the NSE system to make sure that we start this off with a sound understanding of the architecture since it is the foundation of writing the scripts. NSE scripts work almost like a plugin system, and with plugin systems, they expect you to understand and follow certain design principles.
Overview of the NSE System
The Nmap Scripting Engine, or NSE for short, was a system introduced to allow Nmap to make use of external Lua scripts. These scripts will have the extension .nse instead of .lua. Nmap has various phases in the scan that it can execute these scripts and uses a rule or rules to determine if it should run the script at those various phases. If the rule triggers that causes the script to run, the action function in the script is executed. This allows users to extend Nmap and make it more useful, while leveraging data that Nmap has collected during the scan to steer some of the decision making. Scripts can also add information into Nmap's data collection. For example, a script might collect more detailed information about the version or host and provide that into the data store about that host.
A nice feature of this is that this output can be displayed to the user who is already attempting to gather information about a host, and this information will also be collected in Nmap's output files, which can help with the XML file since it can be parsed!
Nmap also provides a collection of libraries to help with a lot of the heavy lifting of talking to various protocols. They can also help provide ease-of-use functions and normalization of data structures.
Architecture of an NSE Script
When writing an NSE Script, there are parts that must be included in the script as Nmap expects these to be present. In short, we can think of these as three parts: the head or header information, the rule, and the action.
The Header: Description, Documentation, and Metadata
The header section has a few parts designed to explain what the script is, provide documentation, and metadata about the script.
The Description
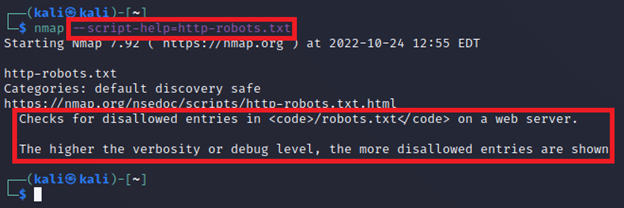
The first part that needs to be included in your script is a description which provides an explanation of what the script does. For example, this is the description from the http-robots.txt.nse script.
description = [[ Checks for disallowed entries in <code>/robots.txt</code> on a web server. The higher the verbosity or debug level, the more disallowed entries are shown. ]]
This is designed to explain what the script does if the user requests this information. The screenshot below shows where this is displayed if the user runs nmap --script-help=http-robots.txt.
Documentation
NSE scripts should include a docstring as well. This will start with three dashes and each following line just uses two dashes. There are some @keyword values you can include to specify information with. However, the biggest one to know is @output, which shows what the user can expect to see as output. Continuing with the http-robots.txt script, this is done with the following code:
--- --@output -- 80/tcp open http syn-ack -- | http-robots.txt: 156 disallowed entries (40 shown) -- | /news?output=xhtml& /search /groups /images /catalogs -- | /catalogues /news /nwshp /news?btcid=*& /news?btaid=*& -- | /setnewsprefs? /index.html? /? /addurl/image? /pagead/ /relpage/ -- | /relcontent /sorry/ /imgres /keyword/ /u/ /univ/ /cobrand /custom -- | /advanced_group_search /googlesite /preferences /setprefs /swr /url /default -- | /m? /m/? /m/lcb /m/news? /m/setnewsprefs? /m/search? /wml? -- |_ /wml/? /wml/search?
Other Metadata
There are three other common values you will want to fill out here which are used by Nmap. Those are the author, license, and categories variables. These provide information metadata about the script. Continuing to use the http-robots.txt script, this is done with the following code:
author = "Eddie Bell"
license = "Same as Nmap--See https://nmap.org/book/man-legal.html"
categories = {"default", "discovery", "safe"}
The author and license are pretty straightforward. These are just strings. The license string shown here is usually the default by most authors. The categories are an array of category strings. You can actually add your own if you want, but it is recommended that you stick to the defaults provided by Nmap. These categories help to explain the nature of the script, but categories can also be provided to the --script= parameter of Nmap to run all of the scripts that match that category in the script database (use the --updatedb to update the database when you install new scripts). The default script categories of Nmap are: auth, broadcast, brute, default, discovery, dos, exploit, external, fuzzer, intrusive, malware, safe, version, and vuln. Detailed descriptions and example scripts for each category can be found in the Nmap documentation.
The Rule(s): Determining if the Script Should Run
The rule or rules of a script provide a function that should return true or false to determine if the script should be executed. An NSE script can have more than one rule if it wants to (example: ssh-hostkey script has a portrule and postrule), but in general, Nmap recognizes the following 4 different rules:
prerule(): This rule is checked BEFORE Nmap has started scanning any hosts. This is usually useful for discovery scripts.hostrule(host): This rule is checked after each batch of hosts is scanned. This is useful if you have a script that only cares about hosts.portrule(host, port): This rule is checked after each batch of hosts is scanned.postrule(): This rule is checked after the scan has completed. This is useful if the script is looking to review the full results of the scan.
To make life easier, the NSE library provides a helper called shortport. This provides some simple helper functions that can make it easier to implement common rule checks and standardize these so we aren't constantly reinventing the wheel. For example, the http-robots.txt script sets its rule with the following code:
portrule = shortport.http
The shortport.http helper will match likely HTTP services. However, there are also some others that are pretty intuitively named such as:
port_or_service(ports, services, protos, states)port_range(range)portnumber(ports, protos, states)service(services, protos, states)ssl(host, port)version_port_or_service(ports, services, protos, states, rarity)
Want to see this in action?
Once you understand the architecture, the next step is building something real. Check out our walkthrough on writing an NSE script for WordPress version detection.
Read: NSE Scripting By ExampleThe Action: What to Do if the Script is Triggered
NSE expects the script to provide a function named action that will be run if the rule returns true. This would normally be implemented in code as:
action = function(host, port) -- TODO: Put your code here. end
Note that the action function parameters can change and SHOULD match your rule's function signature. The return value of the action may be a table of name-value pairs, a string, or nil. Usually, you should aim for a table if you can as this is nicely laid out in the XML report. Strings are useful if the data returned will be really short. This can still show up on the XML report under the script node as an attribute called output.
Conclusion
This blog was designed to lay the foundation of how NSE scripts are structured. Hopefully this information was useful and can help to understand the layout of NSE scripts. With that understanding, you can review the source code of some of the scripts found on https://nmap.org/nsedoc/scripts/ to test your understanding.
Need a team that builds its own tools?
Our testers write custom scripts, build tailored tooling, and go beyond automated scanners to find what actually matters in your environment. If you need a real penetration test, not a scan report, reach out.
Reach Out