🎵 On the tenth day, be cautious when shopping with ten lords a-cautious shopping. Stick to reputable websites, use secure payment methods, and double-check the website's URL to avoid falling victim to online scams during your holiday shopping spree.
The ten lords a-cautious shopping stand as sentinels in the vast digital marketplace, guiding you through the pitfalls of holiday shopping. In the melody of online transactions, these lords emphasize the importance of caution. Choosing reputable websites ensures that your purchases are from trusted sources. These lords serve as wise advisers, urging you to tread carefully in this boundless marketplace, avoiding the snares of potential scams.
As you embark on your holiday shopping spree, let the tenth day be a reminder to follow the lead of the ten lords. Stick to secure payment methods, such as credit cards or well-established online payment platforms, to add an extra layer of protection to your transactions. The lords' wisdom encourages you to double-check the website's URL, ensuring that you're on a legitimate site and not a fraudulent imitation seeking to compromise your financial information.
This tenth day is a call to mindfulness in the digital marketplace, inviting you to dance through your holiday shopping with the grace of the ten lords a-cautious shopping. By exercising caution and adopting these security measures, you ensure that your online shopping experience remains a joyous affair, free from the dissonance of potential cyber threats.
Our training and PCI DSS ASV Scanning serve as your vigilant mentors, imparting wisdom on the importance of cautious shopping. Just as the lords advise, our training programs educate on sticking to reputable websites, using secure payment methods, and double-checking website URLs to sidestep potential online scams. Take a look into our class Introduction to PCI.
Related Resources

Training,
incident response,
cybersecurity
Rolling for Resilience Part 5 - Side Quests: Not Every Member of the Party Swings a Sword!
This is the fifth post in this series addressing my perspective on the current state of Cybersecurity Incident Response ...
Learn More
cybersecurity,
social engineering,
MFA,
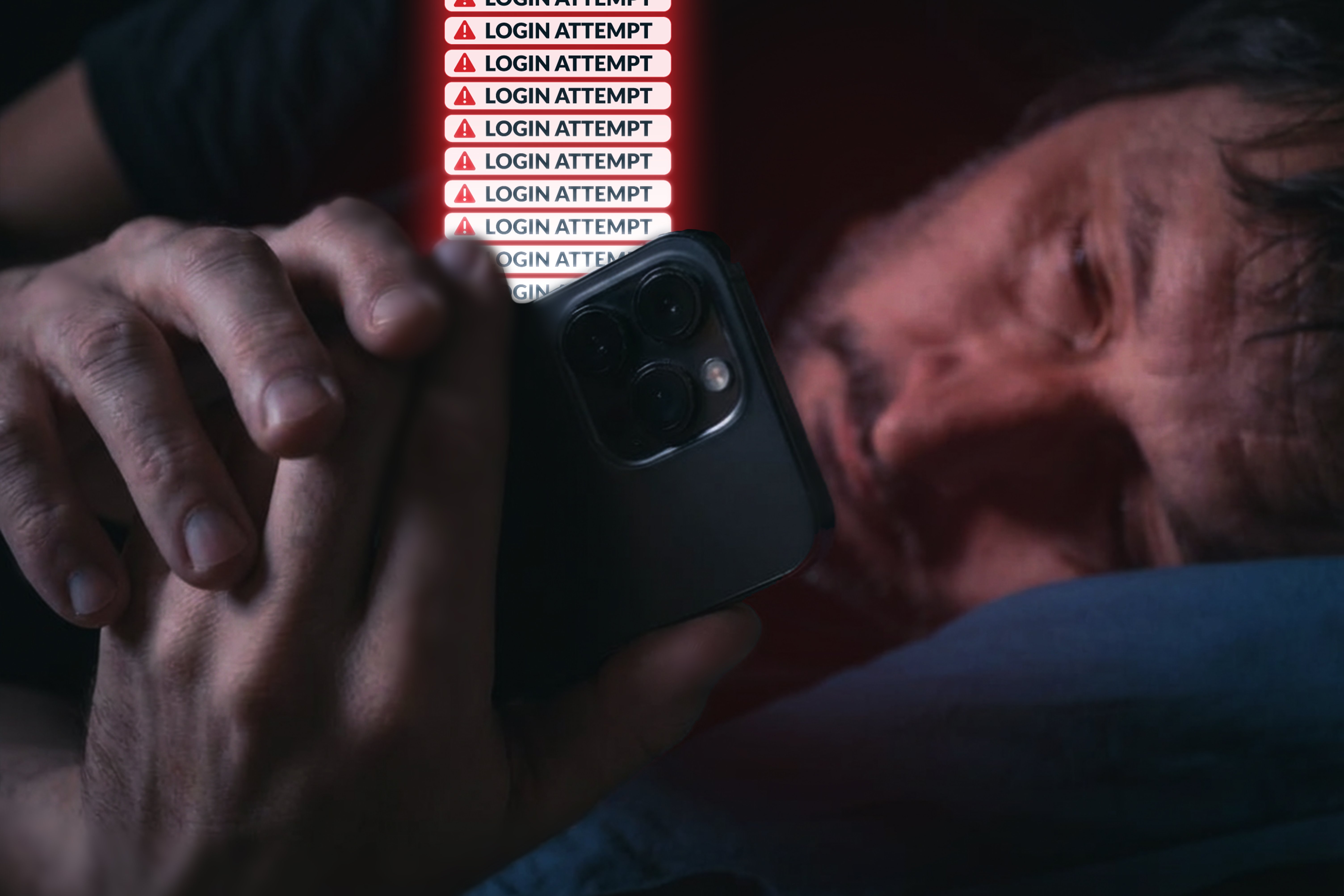
Push Notification Attack
Understanding MFA Fatigue Attacks
Multi-factor authentication has become one of the most widely recommended controls in security. The premise is simple: ...
Learn More

Training,
incident response,
cybersecurity
Rolling for Resilience Part 4 - Boots in the Field: Manuals for Real-Time Action
This is the fourth post in this series addressing my perspective on the current state of Cybersecurity Incident ...
Learn More

